Compare commits
15 Commits
| Author | SHA1 | Date | |
|---|---|---|---|
| ba76f842bb | |||
| 87e83b3bbe | |||
| a94ad50b93 | |||
| a577c80cc3 | |||
| 66cf103bca | |||
| 53f936a2c6 | |||
| 6f4c3e0486 | |||
| b66ae97a0d | |||
| 2ced125e9f | |||
| fb2f52c8ea | |||
| 91d66e6525 | |||
| 8fe7531bf4 | |||
| b2764880a8 | |||
| 0668e1a34a | |||
| 4e063a2268 |
@@ -0,0 +1 @@
|
||||
tidelift: "pypi/django-mfa2"
|
||||
@@ -1,5 +1,15 @@
|
||||
# Change Log
|
||||
|
||||
## 2.1.0
|
||||
* Added Support for Touch ID for Mac OSx and iOS 14 on Safari
|
||||
|
||||
## 2.0.5
|
||||
* Fixed issue in __version__
|
||||
|
||||
## 2.0.4
|
||||
* Fixed: Closes #30
|
||||
|
||||
|
||||
## 2.0.3
|
||||
* Fixed: __version__ to show correct version
|
||||
|
||||
|
||||
@@ -1,9 +1,15 @@
|
||||
# django-mfa2
|
||||
A Django app that handles MFA, it supports TOTP, U2F, FIDO2 U2F (Web Authn), Email Tokens , and Trusted Devices
|
||||
|
||||
### Pip Stats
|
||||
[](https://badge.fury.io/py/django-mfa2)
|
||||
[](https://pepy.tech/project/django-mfa2)
|
||||
|
||||
### Conda Stats
|
||||
[](https://anaconda.org/conda-forge/django-mfa2)
|
||||
[](https://anaconda.org/conda-forge/django-mfa2)
|
||||
[](https://anaconda.org/conda-forge/django-mfa2)
|
||||
|
||||
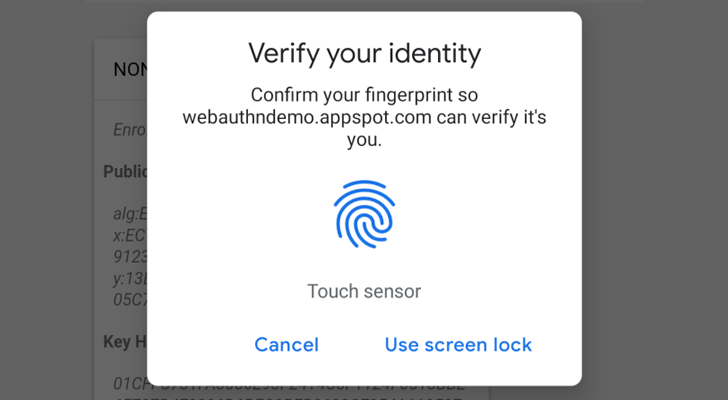
Web Authencation API (WebAuthn) is state-of-the art techology that is expected to replace passwords.
|
||||
|
||||
|
||||
@@ -11,17 +17,17 @@ Web Authencation API (WebAuthn) is state-of-the art techology that is expected t
|
||||
For FIDO2, the following are supported
|
||||
* **security keys** (Firefox 60+, Chrome 67+, Edge 18+, Safari 13 on Mac OS, Chrome on Andriod, Safari on iOS 13.3+),
|
||||
* **Windows Hello** (Firefox 67+, Chrome 72+ , Edge) ,
|
||||
* **Apple's Touch ID** (Chrome 70+ on Mac OS X ),
|
||||
* **Apple's Touch ID/Face ID** (Chrome 70+ on Mac OS X, Safari on macOS Big Sur, Safari on iOS 14.0+ ),
|
||||
* **android-safetynet** (Chrome 70+, Firefox 68+)
|
||||
* **NFC devices using PCSC** (Not Tested, but as supported in fido2)
|
||||
|
||||
In English :), It allows you to verify the user by security keys on PC, Laptops or Mobiles, Windows Hello (Fingerprint, PIN) on Windows 10 Build 1903+ (May 2019 Update) Touch ID on Macbooks (Chrome) and Fingerprint/Face/Iris/PIN on Andriod Phones.
|
||||
In English :), It allows you to verify the user by security keys on PC, Laptops or Mobiles, Windows Hello (Fingerprint, PIN) on Windows 10 Build 1903+ (May 2019 Update) Touch/Face ID on Macbooks (Chrome, Safari), Touch/Face ID on iPhone and iPad and Fingerprint/Face/Iris/PIN on Android Phones.
|
||||
|
||||
Trusted device is a mode for the user to add a device that doesn't support security keys like iOS and andriod without fingerprints or NFC.
|
||||
Trusted device is a mode for the user to add a device that doesn't support security keys like Android without fingerprints or NFC.
|
||||
|
||||
**Note**: `U2F and FIDO2 can only be served under secure context (https)`
|
||||
|
||||
Package tested with Django 1.8, Django 2.1 on Python 2.7 and Python 3.5+ but it was not checked with any version in between but open for issues.
|
||||
Package tested with Django 1.8, Django 2.2 on Python 2.7 and Python 3.5+ but it was not checked with any version in between but open for issues.
|
||||
|
||||
Depends on
|
||||
|
||||
@@ -30,11 +36,23 @@ Depends on
|
||||
* ua-parser
|
||||
* user-agents
|
||||
* python-jose
|
||||
* fido2==0.8.1
|
||||
|
||||
* fido2==0.9.0
|
||||
|
||||
# Installation
|
||||
1. `pip install django-mfa2`
|
||||
1. using pip
|
||||
|
||||
`pip install django-mfa2`
|
||||
2. Using Conda forge
|
||||
|
||||
`conda config --add channels conda-forge`
|
||||
|
||||
`conda install django-mfa2`
|
||||
|
||||
For more info, see the conda-forge repo (https://github.com/conda-forge/django-mfa2-feedstock)
|
||||
|
||||
Thanks for [swainn](https://github.com/swainn) for adding package to conda-forge
|
||||
|
||||
# Usage
|
||||
1. in your settings.py add the application to your installed apps
|
||||
```python
|
||||
INSTALLED_APPS=(
|
||||
@@ -160,3 +178,7 @@ function some_func() {
|
||||
* [swainn](https://github.com/swainn)
|
||||
* [unramk](https://github.com/unramk)
|
||||
* [willingham](https://github.com/willingham)
|
||||
|
||||
|
||||
# Security contact information
|
||||
To report a security vulnerability, please use the [Tidelift security contact](https://tidelift.com/security). Tidelift will coordinate the fix and disclosure.
|
||||
|
||||
+1
-1
@@ -1 +1 @@
|
||||
__version__="2.0.3"
|
||||
__version__="2.1.0"
|
||||
|
||||
+3
-2
@@ -2,8 +2,9 @@ from django.db import models
|
||||
from jsonfield import JSONField
|
||||
from jose import jwt
|
||||
from django.conf import settings
|
||||
from jsonLookup import shasLookup
|
||||
from jsonLookup import shasLookup, hasLookup
|
||||
JSONField.register_lookup(shasLookup)
|
||||
JSONField.register_lookup(hasLookup)
|
||||
|
||||
class User_Keys(models.Model):
|
||||
username=models.CharField(max_length = 50)
|
||||
@@ -24,4 +25,4 @@ class User_Keys(models.Model):
|
||||
def __str__(self):
|
||||
return self.__unicode__()
|
||||
class Meta:
|
||||
app_label='mfa'
|
||||
app_label='mfa'
|
||||
|
||||
Vendored
+9
File diff suppressed because one or more lines are too long
@@ -2,6 +2,7 @@
|
||||
{% load static %}
|
||||
{% block head %}
|
||||
<script type="application/javascript" src="{% static 'mfa/js/cbor.js'%}"></script>
|
||||
<script type="application/javascript" src="{% static 'mfa/js/ua-parser.min.js'%}"></script>
|
||||
<script type="application/javascript">
|
||||
function begin_reg(){
|
||||
fetch('{% url 'fido2_begin_reg' %}',{}).then(function(response) {
|
||||
@@ -40,7 +41,17 @@
|
||||
$("#res").html("<div class='alert alert-danger'>Registeration Failed as " +reason +", <a href='javascript:void(0)' onclick='begin_reg()'> try again </a> or <a href='{% url 'mfa_home' %}'> Go to Security Home</a></div>")
|
||||
})
|
||||
}
|
||||
$(document).ready(setTimeout(begin_reg,500))
|
||||
$(document).ready(function (){
|
||||
ua=new UAParser().getResult()
|
||||
if (ua.browser.name == "Safari")
|
||||
{
|
||||
$("#res").html("<button class='btn btn-success' onclick='begin_reg()'>Start...</button>")
|
||||
}
|
||||
else
|
||||
{
|
||||
setTimeout(begin_reg, 500)
|
||||
}
|
||||
})
|
||||
</script>
|
||||
|
||||
{% endblock %}
|
||||
@@ -55,8 +66,8 @@
|
||||
<div class="panel-body">
|
||||
|
||||
|
||||
<div class="row alert alert-pr" id="res">
|
||||
<p style="color: green">Your broswer should ask you to confirm you indentity.</p>
|
||||
<div class="row alert alert-pr" id="res" align="center">
|
||||
<p style="color: green">Your browser should ask you to confirm you identity.</p>
|
||||
|
||||
</div>
|
||||
</div>
|
||||
|
||||
@@ -1,5 +1,6 @@
|
||||
{% load static %}
|
||||
<script type="application/javascript" src="{% static 'mfa/js/cbor.js' %}"></script>
|
||||
<script type="application/javascript" src="{% static 'mfa/js/ua-parser.min.js' %}"></script>
|
||||
<div class="row">
|
||||
|
||||
<div class="col-sm-10 col-sm-offset-1 col-xs-12 col-md-10 col-md-offset-1 col-lg-8 col-lg-offset-2">
|
||||
@@ -17,7 +18,9 @@
|
||||
<br/>
|
||||
|
||||
{% endif %}
|
||||
<p style="color: green">please press the button on your security key to prove it is you.</p>
|
||||
<div id="res">
|
||||
<p style="color: green">please press the button on your security key to prove it is you.</p>
|
||||
</div>
|
||||
<div id="msgdiv"></div>
|
||||
{% if mode == "auth" %}
|
||||
<form id="u2f_login" action="{% url 'fido2_complete_auth' %}" method="post" enctype="multipart/form-data">
|
||||
@@ -101,7 +104,11 @@
|
||||
$("#main_paragraph").addClass("alert alert-danger")
|
||||
$("#main_paragraph").html("FIDO2 must work under secure context")
|
||||
} else {
|
||||
authen()
|
||||
ua=new UAParser().getResult()
|
||||
if (ua.browser.name == "Safari")
|
||||
$("#res").html("<button class='btn btn-success' onclick='authen()'>Authenticate...</button>")
|
||||
else
|
||||
authen()
|
||||
}
|
||||
});
|
||||
|
||||
|
||||
@@ -4,7 +4,7 @@ from setuptools import find_packages, setup
|
||||
|
||||
setup(
|
||||
name='django-mfa2',
|
||||
version='2.0.3',
|
||||
version='2.1.0',
|
||||
description='Allows user to add 2FA to their accounts',
|
||||
long_description=open("README.md").read(),
|
||||
long_description_content_type="text/markdown",
|
||||
@@ -24,12 +24,12 @@ setup(
|
||||
'ua-parser',
|
||||
'user-agents',
|
||||
'python-jose',
|
||||
'fido2 == 0.8.1',
|
||||
'fido2 == 0.9',
|
||||
'jsonLookup'
|
||||
],
|
||||
python_requires=">=3.5",
|
||||
include_package_data=True,
|
||||
zip_safe=False, # because we're including static files
|
||||
zip_safe=False, # because we're including static files
|
||||
classifiers=[
|
||||
"Development Status :: 5 - Production/Stable",
|
||||
"Environment :: Web Environment",
|
||||
|
||||
Reference in New Issue
Block a user