Compare commits
47 Commits
| Author | SHA1 | Date | |
|---|---|---|---|
|
|
b66ae97a0d | ||
|
|
2ced125e9f | ||
|
|
fb2f52c8ea | ||
|
|
91d66e6525 | ||
|
|
8fe7531bf4 | ||
|
|
b2764880a8 | ||
|
|
0668e1a34a | ||
|
|
4e063a2268 | ||
|
|
049b174a20 | ||
|
|
becfc9e238 | ||
|
|
dda82e5e2e | ||
|
|
9455c501d4 | ||
|
|
4a772ee626 | ||
|
|
5b97d5aa6d | ||
|
|
f3483868ed | ||
|
|
f5218bdbdb | ||
|
|
d9bc0dd5fd | ||
|
|
4b19d95a7e | ||
|
|
01a2766ef5 | ||
|
|
c34efd6ba9 | ||
|
|
d48e464c16 | ||
|
|
b5b308a757 | ||
|
|
d00083a0cf | ||
|
|
9277819787 | ||
|
|
f7baa822f7 | ||
|
|
d404dc6bee | ||
|
|
56eb8821af | ||
|
|
e79411d04c | ||
|
|
d9590c0ea1 | ||
|
|
b6f8696081 | ||
|
|
c5b62ada65 | ||
|
|
55375f7002 | ||
|
|
b6992d3ced | ||
|
|
3d37d0a51f | ||
|
|
a820206a24 | ||
|
|
bc407ca39b | ||
|
|
9786f4a888 | ||
|
|
804b76518e | ||
|
|
91d08cdafc | ||
|
|
7ee2281785 | ||
|
|
288ab96425 | ||
|
|
36e9bf154a | ||
|
|
0b0a3230fa | ||
|
|
5d31b83fae | ||
|
|
c134cd87e2 | ||
|
|
ab4b1fdf5a | ||
|
|
2d5b507a50 |
1
.github/FUNDING.yml
vendored
Normal file
1
.github/FUNDING.yml
vendored
Normal file
@@ -0,0 +1 @@
|
||||
tidelift: "pypi/django-mfa2"
|
||||
11
.github/dependabot.yml
vendored
Normal file
11
.github/dependabot.yml
vendored
Normal file
@@ -0,0 +1,11 @@
|
||||
# To get started with Dependabot version updates, you'll need to specify which
|
||||
# package ecosystems to update and where the package manifests are located.
|
||||
# Please see the documentation for all configuration options:
|
||||
# https://help.github.com/github/administering-a-repository/configuration-options-for-dependency-updates
|
||||
|
||||
version: 2
|
||||
updates:
|
||||
- package-ecosystem: "pip" # See documentation for possible values
|
||||
directory: "/" # Location of package manifests
|
||||
schedule:
|
||||
interval: "daily"
|
||||
36
CHANGELOG.md
36
CHANGELOG.md
@@ -1,5 +1,41 @@
|
||||
# Change Log
|
||||
|
||||
## 2.0.5
|
||||
* Fixed issue in __version__
|
||||
|
||||
## 2.0.4
|
||||
* Fixed: Closes #30
|
||||
|
||||
|
||||
## 2.0.3
|
||||
* Fixed: __version__ to show correct version
|
||||
|
||||
## 2.0.2
|
||||
* Added: A missing migration
|
||||
thnks to @swainn
|
||||
|
||||
## 2.0.1
|
||||
* Fixed: issue in migration between Postgres and SQLite
|
||||
thnks to @swainn and @willingham
|
||||
|
||||
## 2.0
|
||||
* Dropped support to djangp-1.8 and Python 2.7
|
||||
* Added: never-cache decorator
|
||||
* Fixes to Make Email Method More Robust
|
||||
* Addresses several structure and style issues with TOTP and Email dialogs
|
||||
* Updated to fido2 0.8.1
|
||||
|
||||
Thanks to @swainn
|
||||
|
||||
## v1.9.1
|
||||
* Fixed: is_authenticated #13
|
||||
* Fixed: is_anonymous #6
|
||||
|
||||
thanks to @d3cline,
|
||||
|
||||
## v1.7
|
||||
* Better Error Management
|
||||
* Better Token recheck
|
||||
## v 1.6.0
|
||||
* Fixed some issues for django>= 2.0
|
||||
* Added example app.
|
||||
|
||||
42
README.md
42
README.md
@@ -1,17 +1,24 @@
|
||||
# django-mfa2
|
||||
A Django app that handles MFA, it supports TOTP, U2F, FIDO2 U2F (Web Authn), Email Tokens , and Trusted Devices
|
||||
|
||||
### Pip Stats
|
||||
[](https://badge.fury.io/py/django-mfa2)
|
||||
[](https://pepy.tech/project/django-mfa2)
|
||||
|
||||
### Conda Stats
|
||||
[](https://anaconda.org/conda-forge/django-mfa2)
|
||||
[](https://anaconda.org/conda-forge/django-mfa2)
|
||||
[](https://anaconda.org/conda-forge/django-mfa2)
|
||||
|
||||
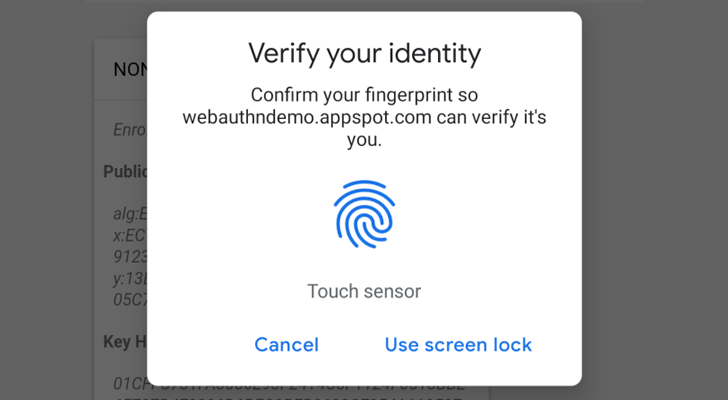
Web Authencation API (WebAuthn) is state-of-the art techology that is expected to replace passwords.
|
||||
|
||||
|
||||
|
||||
For FIDO2, the following are supported
|
||||
* **security keys** (Firefox 60+, Chrome 67+, Edge 18+),
|
||||
* **security keys** (Firefox 60+, Chrome 67+, Edge 18+, Safari 13 on Mac OS, Chrome on Andriod, Safari on iOS 13.3+),
|
||||
* **Windows Hello** (Firefox 67+, Chrome 72+ , Edge) ,
|
||||
* **Apple's Touch ID** (Chrome 70+ on Mac OS X ),
|
||||
* **android-safetynet** (Chrome 70+)
|
||||
* **android-safetynet** (Chrome 70+, Firefox 68+)
|
||||
* **NFC devices using PCSC** (Not Tested, but as supported in fido2)
|
||||
|
||||
In English :), It allows you to verify the user by security keys on PC, Laptops or Mobiles, Windows Hello (Fingerprint, PIN) on Windows 10 Build 1903+ (May 2019 Update) Touch ID on Macbooks (Chrome) and Fingerprint/Face/Iris/PIN on Andriod Phones.
|
||||
@@ -29,11 +36,23 @@ Depends on
|
||||
* ua-parser
|
||||
* user-agents
|
||||
* python-jose
|
||||
* fido2==0.7
|
||||
|
||||
* fido2==0.8.1
|
||||
|
||||
# Installation
|
||||
1. `pip install django-mfa2`
|
||||
1. using pip
|
||||
|
||||
`pip install django-mfa2`
|
||||
2. Using Conda forge
|
||||
|
||||
`conda config --add channels conda-forge`
|
||||
|
||||
`conda install django-mfa2`
|
||||
|
||||
For more info, see the conda-forge repo (https://github.com/conda-forge/django-mfa2-feedstock)
|
||||
|
||||
Thanks for [swainn](https://github.com/swainn) for adding package to conda-forge
|
||||
|
||||
# Usage
|
||||
1. in your settings.py add the application to your installed apps
|
||||
```python
|
||||
INSTALLED_APPS=(
|
||||
@@ -53,7 +72,7 @@ Depends on
|
||||
MFA_RECHECK_MAX=30 # Maximum in seconds
|
||||
MFA_QUICKLOGIN=True # Allow quick login for returning users by provide only their 2FA
|
||||
MFA_HIDE_DISABLE=('FIDO2',) # Can the user disable his key (Added in 1.2.0).
|
||||
MFA_OWNED_BY_ENTERPRISE = FALSE # Who ownes security keys
|
||||
MFA_OWNED_BY_ENTERPRISE = FALSE # Who owns security keys
|
||||
|
||||
TOKEN_ISSUER_NAME="PROJECT_NAME" #TOTP Issuer name
|
||||
|
||||
@@ -152,3 +171,14 @@ function some_func() {
|
||||
}
|
||||
|
||||
````
|
||||
|
||||
# Contributors
|
||||
* [mahmoodnasr](https://github.com/mahmoodnasr)
|
||||
* [d3cline](https://github.com/d3cline)
|
||||
* [swainn](https://github.com/swainn)
|
||||
* [unramk](https://github.com/unramk)
|
||||
* [willingham](https://github.com/willingham)
|
||||
|
||||
|
||||
# Security contact information
|
||||
To report a security vulnerability, please use the [Tidelift security contact](https://tidelift.com/security). Tidelift will coordinate the fix and disclosure.
|
||||
|
||||
@@ -77,8 +77,10 @@ WSGI_APPLICATION = 'example.wsgi.application'
|
||||
|
||||
DATABASES = {
|
||||
'default': {
|
||||
'ENGINE': 'django.db.backends.sqlite3',
|
||||
'NAME': os.path.join(BASE_DIR, 'db.sqlite3'),
|
||||
'ENGINE': 'django.db.backends.mysql',
|
||||
'NAME': 'mfa',
|
||||
'USER': 'root',
|
||||
'PASSWORD': 'password',
|
||||
}
|
||||
}
|
||||
|
||||
|
||||
@@ -2,7 +2,10 @@ from django.conf import settings
|
||||
from django.core.mail import EmailMessage
|
||||
|
||||
def send(to,subject,body):
|
||||
From = "%s <%s>" % (settings.EMAIL_FROM, settings.EMAIL_HOST_USER)
|
||||
from_email_address = settings.EMAIL_HOST_USER
|
||||
if '@' not in from_email_address:
|
||||
from_email_address = settings.DEFAULT_FROM_EMAIL
|
||||
From = "%s <%s>" % (settings.EMAIL_FROM, from_email_address)
|
||||
email = EmailMessage(subject,body,From,to)
|
||||
email.content_subtype = "html"
|
||||
return email.send(False)
|
||||
@@ -1,4 +1,5 @@
|
||||
from django.shortcuts import render
|
||||
from django.views.decorators.cache import never_cache
|
||||
from django.template.context_processors import csrf
|
||||
import datetime,random
|
||||
from random import randint
|
||||
@@ -13,8 +14,9 @@ def sendEmail(request,username,secret):
|
||||
kwargs = {key: username}
|
||||
user = User.objects.get(**kwargs)
|
||||
res=render(request,"mfa_email_token_template.html",{"request":request,"user":user,'otp':secret})
|
||||
return send([user.email],"OTP", str(res.content))
|
||||
return send([user.email],"OTP", res.content.decode())
|
||||
|
||||
@never_cache
|
||||
def start(request):
|
||||
context = csrf(request)
|
||||
if request.method == "POST":
|
||||
@@ -36,6 +38,7 @@ def start(request):
|
||||
if sendEmail(request, request.user.username, request.session["email_secret"]):
|
||||
context["sent"] = True
|
||||
return render(request,"Email/Add.html", context)
|
||||
@never_cache
|
||||
def auth(request):
|
||||
context=csrf(request)
|
||||
if request.method=="POST":
|
||||
|
||||
10
mfa/FIDO2.py
10
mfa/FIDO2.py
@@ -1,5 +1,5 @@
|
||||
from fido2.client import ClientData
|
||||
from fido2.server import Fido2Server, RelyingParty
|
||||
from fido2.server import Fido2Server, PublicKeyCredentialRpEntity
|
||||
from fido2.ctap2 import AttestationObject, AuthenticatorData
|
||||
from django.template.context_processors import csrf
|
||||
from django.views.decorators.csrf import csrf_exempt
|
||||
@@ -24,7 +24,7 @@ def recheck(request):
|
||||
|
||||
|
||||
def getServer():
|
||||
rp = RelyingParty(settings.FIDO_SERVER_ID, settings.FIDO_SERVER_NAME)
|
||||
rp = PublicKeyCredentialRpEntity(settings.FIDO_SERVER_ID, settings.FIDO_SERVER_NAME)
|
||||
return Fido2Server(rp)
|
||||
def begin_registeration(request):
|
||||
server = getServer()
|
||||
@@ -136,7 +136,11 @@ def authenticate_complete(request):
|
||||
mfa["next_check"] = int((datetime.datetime.now()+ datetime.timedelta(
|
||||
seconds=random.randint(settings.MFA_RECHECK_MIN, settings.MFA_RECHECK_MAX))).strftime("%s"))
|
||||
request.session["mfa"] = mfa
|
||||
if not request.user.is_authenticated():
|
||||
try:
|
||||
authenticated=request.user.is_authenticated
|
||||
except:
|
||||
authenticated = request.user.is_authenticated()
|
||||
if not authenticated:
|
||||
res=login(request)
|
||||
if not "location" in res: return reset_cookie(request)
|
||||
return HttpResponse(simplejson.dumps({'status':"OK","redirect":res["location"]}),content_type="application/json")
|
||||
|
||||
@@ -1 +1 @@
|
||||
__version__="1.6.0"
|
||||
__version__="2.0.5"
|
||||
|
||||
@@ -4,6 +4,12 @@ from __future__ import unicode_literals
|
||||
from django.db import models, migrations
|
||||
from django.conf import settings
|
||||
|
||||
|
||||
def update_owned_by_enterprise(apps, schema_editor):
|
||||
user_keys = apps.get_model('mfa', 'user_keys')
|
||||
user_keys.objects.filter(key_type='FIDO2').update(owned_by_enterprise=getattr(settings,"MFA_OWNED_BY_ENTERPRISE",False))
|
||||
|
||||
|
||||
class Migration(migrations.Migration):
|
||||
|
||||
dependencies = [
|
||||
@@ -16,5 +22,5 @@ class Migration(migrations.Migration):
|
||||
name='owned_by_enterprise',
|
||||
field=models.NullBooleanField(default=None),
|
||||
),
|
||||
migrations.RunSQL("update mfa_user_keys set owned_by_enterprise = %s where key_type='FIDO2'"%(1 if getattr(settings,"MFA_OWNED_BY_ENTERPRISE",False) else 0 ))
|
||||
migrations.RunPython(update_owned_by_enterprise)
|
||||
]
|
||||
|
||||
18
mfa/migrations/0010_auto_20201110_0557.py
Normal file
18
mfa/migrations/0010_auto_20201110_0557.py
Normal file
@@ -0,0 +1,18 @@
|
||||
# Generated by Django 2.0 on 2020-11-10 05:57
|
||||
|
||||
from django.db import migrations, models
|
||||
|
||||
|
||||
class Migration(migrations.Migration):
|
||||
|
||||
dependencies = [
|
||||
('mfa', '0009_user_keys_owned_by_enterprise'),
|
||||
]
|
||||
|
||||
operations = [
|
||||
migrations.AlterField(
|
||||
model_name='user_keys',
|
||||
name='key_type',
|
||||
field=models.CharField(default='TOTP', max_length=25),
|
||||
),
|
||||
]
|
||||
@@ -4,6 +4,7 @@ from jose import jwt
|
||||
from django.conf import settings
|
||||
from jsonLookup import shasLookup
|
||||
JSONField.register_lookup(shasLookup)
|
||||
JSONField.register_lookup(hasLookup)
|
||||
|
||||
class User_Keys(models.Model):
|
||||
username=models.CharField(max_length = 50)
|
||||
|
||||
@@ -4,16 +4,13 @@
|
||||
{% block content %}
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
<div class="container">
|
||||
<div class="panel panel-default">
|
||||
<div class="panel-heading">
|
||||
<strong> Activate Token by email</strong>
|
||||
</div>
|
||||
<div class="panel-body">
|
||||
|
||||
<FORM METHOD="POST" ACTION="{% url 'start_email' %}" Id="formLogin" onSubmit="" name="FrontPage_Form1">
|
||||
|
||||
|
||||
{% csrf_token %}
|
||||
{% if invalid %}
|
||||
<div class="alert alert-danger">
|
||||
@@ -28,10 +25,9 @@
|
||||
<fieldset>
|
||||
<div class="row">
|
||||
<div class="col-sm-12 col-md-12">
|
||||
<p>Enter the 6-digits sent to your email.</p>
|
||||
<p>Enter the code sent to your email.</p>
|
||||
</div>
|
||||
</div>
|
||||
|
||||
<div class="row">
|
||||
<div class="col-sm-12 col-md-12">
|
||||
<div class="form-group">
|
||||
@@ -40,16 +36,16 @@
|
||||
<i class="glyphicon glyphicon-lock"></i>
|
||||
</span>
|
||||
<input class="form-control" size="6" MaxLength="6" value="" placeholder="e.g 55552" name="otp" type="text" id="otp" autofocus>
|
||||
|
||||
</div>
|
||||
</div>
|
||||
|
||||
<div class="form-group">
|
||||
|
||||
<input type="submit" class="btn btn-lg btn-success btn-block" value="Verify">
|
||||
</div>
|
||||
</div>
|
||||
</div>
|
||||
</fieldset>
|
||||
</FORM>
|
||||
</div>
|
||||
</div>
|
||||
</div>
|
||||
{% endblock %}
|
||||
@@ -39,7 +39,7 @@
|
||||
<fieldset>
|
||||
<div class="row">
|
||||
<div class="col-sm-12 col-md-12">
|
||||
<p>Enter the 6-digits sent to your email.</p>
|
||||
<p>Enter the code sent to your email.</p>
|
||||
</div>
|
||||
</div>
|
||||
|
||||
|
||||
@@ -20,7 +20,7 @@
|
||||
$("#modal-footer").prepend("<button id='actionBtn' class='btn btn-danger' onclick='confirmDel("+id+")'>Confirm Deletion</button>")
|
||||
$("#popUpModal").modal()
|
||||
}
|
||||
{% if not HIDE_DISABLE %}
|
||||
|
||||
function toggleKey(id) {
|
||||
$.ajax({
|
||||
url:"{% url 'toggle_key' %}?id="+id,
|
||||
@@ -34,7 +34,6 @@
|
||||
}
|
||||
})
|
||||
}
|
||||
{% endif %}
|
||||
</script>
|
||||
<link href="{% static 'mfa/css/bootstrap-toggle.min.css' %}" rel="stylesheet">
|
||||
<script src="{% static 'mfa/js/bootstrap-toggle.min.js'%}"></script>
|
||||
@@ -67,7 +66,7 @@
|
||||
{% endif %}
|
||||
</ul>
|
||||
</div>
|
||||
|
||||
</div>
|
||||
<br/>
|
||||
<br/>
|
||||
<table class="table table-striped">
|
||||
|
||||
@@ -70,7 +70,7 @@
|
||||
</div>
|
||||
<div class="row">
|
||||
|
||||
<p>Scan the image below with the two-factor authentication app on your <a href="javascript:void(0)" onclick="showTOTP()">phone/PC</a> phone/PC. If you can’t use a barcode,
|
||||
<p>Scan the image below with the two-factor authentication app on your <a href="javascript:void(0)" onclick="showTOTP()">phone/PC</a>. If you can’t use a barcode,
|
||||
<a href="javascript:void(0)" onclick="showKey()">enter this text</a> instead. </p>
|
||||
</div>
|
||||
|
||||
@@ -93,7 +93,7 @@
|
||||
<input style="display: inline;width: 95%" maxlength="6" size="6" class="form-control" id="answer" placeholder="e.g 785481"/>
|
||||
|
||||
</div>
|
||||
<div class="row">
|
||||
<div class="row" style="padding-top: 10px;">
|
||||
<div class="col-md-6" style="padding-left: 0px">
|
||||
<button class="btn btn-success" onclick="verify()">Enable</button>
|
||||
</div>
|
||||
|
||||
@@ -1,4 +1,5 @@
|
||||
from django.shortcuts import render
|
||||
from django.views.decorators.cache import never_cache
|
||||
from django.http import HttpResponse
|
||||
from .models import *
|
||||
from django.template.context_processors import csrf
|
||||
@@ -31,6 +32,7 @@ def recheck(request):
|
||||
return HttpResponse(simplejson.dumps({"recheck": False}), content_type="application/json")
|
||||
return render(request,"TOTP/recheck.html", context)
|
||||
|
||||
@never_cache
|
||||
def auth(request):
|
||||
context=csrf(request)
|
||||
if request.method=="POST":
|
||||
@@ -68,5 +70,6 @@ def verify(request):
|
||||
return HttpResponse("Success")
|
||||
else: return HttpResponse("Error")
|
||||
|
||||
@never_cache
|
||||
def start(request):
|
||||
return render(request,"TOTP/Add.html",{})
|
||||
|
||||
14
mfa/views.py
14
mfa/views.py
@@ -1,5 +1,5 @@
|
||||
from django.shortcuts import render
|
||||
#from django.http import HttpResponse,HttpResponseRedirect
|
||||
from django.http import HttpResponse,HttpResponseRedirect
|
||||
from .models import *
|
||||
try:
|
||||
from django.urls import reverse
|
||||
@@ -7,10 +7,12 @@ except:
|
||||
from django.core.urlresolvers import reverse
|
||||
from django.template.context_processors import csrf
|
||||
from django.template.context import RequestContext
|
||||
from django.http import HttpResponseRedirect
|
||||
from django.conf import settings
|
||||
from . import TrustedDevice
|
||||
from django.contrib.auth.decorators import login_required
|
||||
from user_agents import parse
|
||||
|
||||
@login_required
|
||||
def index(request):
|
||||
keys=[]
|
||||
context={"keys":User_Keys.objects.filter(username=request.user.username),"UNALLOWED_AUTHEN_METHODS":settings.MFA_UNALLOWED_METHODS
|
||||
@@ -52,6 +54,8 @@ def login(request):
|
||||
callable_func = __get_callable_function__(settings.MFA_LOGIN_CALLBACK)
|
||||
return callable_func(request,username=request.session["base_username"])
|
||||
|
||||
|
||||
@login_required
|
||||
def delKey(request):
|
||||
key=User_Keys.objects.get(id=request.GET["id"])
|
||||
if key.username == request.user.username:
|
||||
@@ -73,18 +77,20 @@ def __get_callable_function__(func_path):
|
||||
raise Exception("Module does not have requested function")
|
||||
return callable_func
|
||||
|
||||
@login_required
|
||||
def toggleKey(request):
|
||||
id=request.GET["id"]
|
||||
q=User_Keys.objects.filter(username=request.user.username, id=id)
|
||||
if q.count()==1:
|
||||
key=q[0]
|
||||
if not key.key_type in settings.MFA_HIDE_DISABLE:
|
||||
key.enabled=not key.enabled
|
||||
key.save()
|
||||
return HttpResponse("OK")
|
||||
else:
|
||||
return HttpResponse("You can't change this method.")
|
||||
else:
|
||||
return HttpResponse("Error")
|
||||
|
||||
def goto(request,method):
|
||||
return HttpResponseRedirect(reverse(method.lower()+"_auth"))
|
||||
|
||||
|
||||
|
||||
@@ -6,6 +6,5 @@ django >= 1.7
|
||||
ua-parser
|
||||
user-agents
|
||||
python-jose
|
||||
fido2 == 0.7
|
||||
fido2 == 0.8.1
|
||||
jsonLookup
|
||||
|
||||
|
||||
18
setup.py
18
setup.py
@@ -4,7 +4,7 @@ from setuptools import find_packages, setup
|
||||
|
||||
setup(
|
||||
name='django-mfa2',
|
||||
version='1.7.11',
|
||||
version='2.0.5',
|
||||
description='Allows user to add 2FA to their accounts',
|
||||
long_description=open("README.md").read(),
|
||||
long_description_content_type="text/markdown",
|
||||
@@ -16,7 +16,7 @@ setup(
|
||||
license='MIT',
|
||||
packages=find_packages(),
|
||||
install_requires=[
|
||||
'django >= 1.7',
|
||||
'django >= 2.0',
|
||||
'jsonfield',
|
||||
'simplejson',
|
||||
'pyotp',
|
||||
@@ -24,32 +24,28 @@ setup(
|
||||
'ua-parser',
|
||||
'user-agents',
|
||||
'python-jose',
|
||||
'fido2 == 0.7',
|
||||
'fido2 == 0.8.1',
|
||||
'jsonLookup'
|
||||
],
|
||||
python_requires=">=2.7, !=3.0.*, !=3.1.*, !=3.2.*, !=3.3.*",
|
||||
python_requires=">=3.5",
|
||||
include_package_data=True,
|
||||
zip_safe=False, # because we're including static files
|
||||
classifiers=[
|
||||
"Development Status :: 5 - Production/Stable",
|
||||
"Environment :: Web Environment",
|
||||
"Framework :: Django",
|
||||
"Framework :: Django :: 1.7",
|
||||
"Framework :: Django :: 1.8",
|
||||
"Framework :: Django :: 1.9",
|
||||
"Framework :: Django :: 1.10",
|
||||
"Framework :: Django :: 1.11",
|
||||
"Framework :: Django :: 2.0",
|
||||
"Framework :: Django :: 2.1",
|
||||
"Framework :: Django :: 2.2",
|
||||
"Intended Audience :: Developers",
|
||||
"Operating System :: OS Independent",
|
||||
"Programming Language :: Python",
|
||||
"Programming Language :: Python :: 2",
|
||||
"Programming Language :: Python :: 2.7",
|
||||
"Programming Language :: Python :: 3",
|
||||
"Programming Language :: Python :: 3.4",
|
||||
"Programming Language :: Python :: 3.5",
|
||||
"Programming Language :: Python :: 3.6",
|
||||
"Programming Language :: Python :: 3.7",
|
||||
"Programming Language :: Python :: 3.8",
|
||||
"Topic :: Software Development :: Libraries :: Python Modules",
|
||||
]
|
||||
)
|
||||
|
||||
Reference in New Issue
Block a user