Compare commits
98 Commits
v1.6
..
Better_TOTP
| Author | SHA1 | Date | |
|---|---|---|---|
| ca49e1623d | |||
| 0b83758625 | |||
| 6d59258393 | |||
| bb88f680a0 | |||
| 62bb50307e | |||
| 68e257d60e | |||
| ba4e7f9a17 | |||
| f4d8934ef5 | |||
| 81675207d3 | |||
| daece24c6d | |||
| f654debb98 | |||
| 3d133b3fff | |||
| 714fb68a65 | |||
| ec16539c34 | |||
| e8ce96c404 | |||
| b18dfe2bb6 | |||
| 84f93444a3 | |||
| 34fcca57c8 | |||
| 174dba2878 | |||
| 0945561136 | |||
| 6b132683a7 | |||
| d54cd20d9b | |||
| 007872bd8a | |||
| 8911a4f0b6 | |||
| 9c126f06b5 | |||
| 7a154cfa34 | |||
| 958775418d | |||
| ef8287666c | |||
| 19563fe2b8 | |||
| 0e7c0911ca | |||
| ebfdaf7504 | |||
| c78e600b37 | |||
| e1e931285f | |||
| 2709e70f88 | |||
| 25fe80d76d | |||
| ba76f842bb | |||
| 87e83b3bbe | |||
| a94ad50b93 | |||
| 75cf1e6130 | |||
| 911be9e106 | |||
| a577c80cc3 | |||
| 66cf103bca | |||
| 53f936a2c6 | |||
| 6f4c3e0486 | |||
| b66ae97a0d | |||
| 2ced125e9f | |||
| fb2f52c8ea | |||
| 91d66e6525 | |||
| 8fe7531bf4 | |||
| b2764880a8 | |||
| 0668e1a34a | |||
| 4e063a2268 | |||
| 049b174a20 | |||
| becfc9e238 | |||
| dda82e5e2e | |||
| 9455c501d4 | |||
| 4a772ee626 | |||
| 5b97d5aa6d | |||
| f3483868ed | |||
| f5218bdbdb | |||
| d9bc0dd5fd | |||
| 4b19d95a7e | |||
| 01a2766ef5 | |||
| c34efd6ba9 | |||
| d48e464c16 | |||
| b5b308a757 | |||
| d00083a0cf | |||
| 9277819787 | |||
| f7baa822f7 | |||
| d404dc6bee | |||
| 56eb8821af | |||
| e79411d04c | |||
| d9590c0ea1 | |||
| b6f8696081 | |||
| c5b62ada65 | |||
| 55375f7002 | |||
| b6992d3ced | |||
| 3d37d0a51f | |||
| a820206a24 | |||
| bc407ca39b | |||
| 9786f4a888 | |||
| 804b76518e | |||
| 91d08cdafc | |||
| 7ee2281785 | |||
| 288ab96425 | |||
| 36e9bf154a | |||
| 0b0a3230fa | |||
| 5d31b83fae | |||
| c134cd87e2 | |||
| ab4b1fdf5a | |||
| 2d5b507a50 | |||
| 7800962eb6 | |||
| 3ac3e101a3 | |||
| 4c31e1815e | |||
| 64dafb8d2e | |||
| 9086f47456 | |||
| 03ab360939 | |||
| 3a85efc1e6 |
@@ -0,0 +1 @@
|
||||
tidelift: "pypi/django-mfa2"
|
||||
@@ -0,0 +1,11 @@
|
||||
# To get started with Dependabot version updates, you'll need to specify which
|
||||
# package ecosystems to update and where the package manifests are located.
|
||||
# Please see the documentation for all configuration options:
|
||||
# https://help.github.com/github/administering-a-repository/configuration-options-for-dependency-updates
|
||||
|
||||
version: 2
|
||||
updates:
|
||||
- package-ecosystem: "pip" # See documentation for possible values
|
||||
directory: "/" # Location of package manifests
|
||||
schedule:
|
||||
interval: "daily"
|
||||
@@ -0,0 +1,13 @@
|
||||
on: [push]
|
||||
jobs:
|
||||
test:
|
||||
runs-on: ubuntu-latest
|
||||
steps:
|
||||
- uses: actions/checkout@v2
|
||||
- name: python
|
||||
run: |
|
||||
sudo apt-get install python3
|
||||
- name: lint
|
||||
run: |
|
||||
pip install black
|
||||
black --check --exclude migrations mfa/ example/ setup.py
|
||||
+59
-4
@@ -1,13 +1,68 @@
|
||||
# Change Log
|
||||
|
||||
## 2.3.0
|
||||
* Some code cleanup thanks to @xi
|
||||
* Added: MFA_TOTP_FAILURE_WINDOW & MFA_TOTP_FAILURE_LIMIT
|
||||
|
||||
## 2.2.0
|
||||
* Added: MFA_REDIRECT_AFTER_REGISTRATION settings parameter
|
||||
* Fixed: Deprecation error for NullBooleanField
|
||||
|
||||
## 2.1.2
|
||||
* Fixed: Getting timestamp on Python 3.7 as ("%s") is raising an exception
|
||||
* Upgraded to FIDO 0.9.1
|
||||
|
||||
|
||||
## 2.1.1
|
||||
* Fixed: FIDO2 version in requirements.txt file.
|
||||
|
||||
## 2.1.0
|
||||
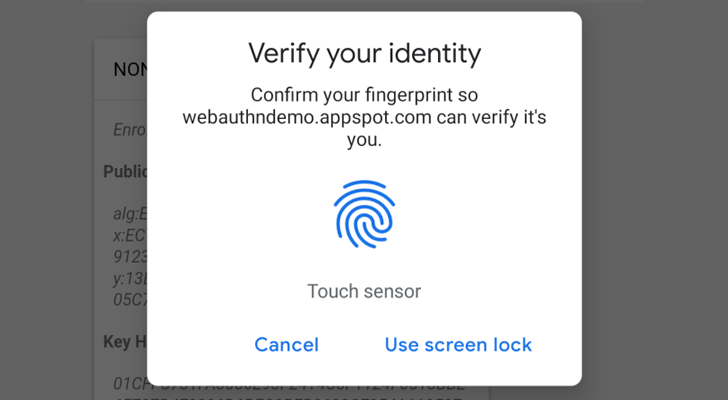
* Added Support for Touch ID for Mac OSx and iOS 14 on Safari
|
||||
|
||||
## 2.0.5
|
||||
* Fixed issue in __version__
|
||||
|
||||
## 2.0.4
|
||||
* Fixed: Closes #30
|
||||
|
||||
|
||||
## 2.0.3
|
||||
* Fixed: __version__ to show correct version
|
||||
|
||||
## 2.0.2
|
||||
* Added: A missing migration
|
||||
thnks to @swainn
|
||||
|
||||
## 2.0.1
|
||||
* Fixed: issue in migration between Postgres and SQLite
|
||||
thnks to @swainn and @willingham
|
||||
|
||||
## 2.0
|
||||
* Dropped support to djangp-1.8 and Python 2.7
|
||||
* Added: never-cache decorator
|
||||
* Fixes to Make Email Method More Robust
|
||||
* Addresses several structure and style issues with TOTP and Email dialogs
|
||||
* Updated to fido2 0.8.1
|
||||
|
||||
Thanks to @swainn
|
||||
|
||||
## v1.9.1
|
||||
* Fixed: is_authenticated #13
|
||||
* Fixed: is_anonymous #6
|
||||
|
||||
thanks to @d3cline,
|
||||
|
||||
## v1.7
|
||||
* Better Error Management
|
||||
* Better Token recheck
|
||||
## v 1.6.0
|
||||
* Fixed some issues for django>= 2.0
|
||||
* Added example app.
|
||||
* Fixed some issues for django>= 2.0
|
||||
* Added example app.
|
||||
|
||||
## v.1.5.0
|
||||
* Added id the key used to validate to the session dictionary as 'id'
|
||||
* Added id the key used to validate to the session dictionary as 'id'
|
||||
## v1.4.0
|
||||
* Updated to FIDO == 0.7
|
||||
* Updated to FIDO == 0.7
|
||||
|
||||
## v1.3.0
|
||||
* Updated to FIDO2 == 0.6
|
||||
|
||||
+1
-1
@@ -5,4 +5,4 @@
|
||||
1. activate env `source venv/bin/activate`
|
||||
1. install requirements `pip install -r requirements.txt`
|
||||
1. migrate `python manage.py migrate`
|
||||
1. create super user 'python manage.py createsuperuser'
|
||||
1. create super user 'python manage.py createsuperuser'
|
||||
@@ -1,26 +1,34 @@
|
||||
# django-mfa2
|
||||
A Django app that handles MFA, it supports TOTP, U2F, FIDO2 U2F (Web Authn), Email Tokens , and Trusted Devices
|
||||
|
||||

|
||||
### Pip Stats
|
||||
[](https://badge.fury.io/py/django-mfa2)
|
||||
[](https://pepy.tech/project/django-mfa2)
|
||||
|
||||
### Conda Stats
|
||||
[](https://anaconda.org/conda-forge/django-mfa2)
|
||||
[](https://anaconda.org/conda-forge/django-mfa2)
|
||||
[](https://anaconda.org/conda-forge/django-mfa2)
|
||||
|
||||
Web Authencation API (WebAuthn) is state-of-the art techology that is expected to replace passwords.
|
||||
|
||||
|
||||
|
||||
For FIDO2, the following are supported
|
||||
* **security keys** (Firefox 60+, Chrome 67+, Edge 18+),
|
||||
* **security keys** (Firefox 60+, Chrome 67+, Edge 18+, Safari 13 on Mac OS, Chrome on Andriod, Safari on iOS 13.3+),
|
||||
* **Windows Hello** (Firefox 67+, Chrome 72+ , Edge) ,
|
||||
* **Apple's Touch ID** (Chrome 70+ on Mac OS X ),
|
||||
* **android-safetynet** (Chrome 70+)
|
||||
* **Apple's Touch ID/Face ID** (Chrome 70+ on Mac OS X, Safari on macOS Big Sur, Safari on iOS 14.0+ ),
|
||||
* **android-safetynet** (Chrome 70+, Firefox 68+)
|
||||
* **NFC devices using PCSC** (Not Tested, but as supported in fido2)
|
||||
|
||||
In English :), It allows you to verify the user by security keys on PC, Laptops or Mobiles, Windows Hello (Fingerprint, PIN) on Windows 10 Build 1903+ (May 2019 Update) Touch ID on Macbooks (Chrome) and Fingerprint/Face/Iris/PIN on Andriod Phones.
|
||||
In English :), It allows you to verify the user by security keys on PC, Laptops or Mobiles, Windows Hello (Fingerprint, PIN) on Windows 10 Build 1903+ (May 2019 Update) Touch/Face ID on Macbooks (Chrome, Safari), Touch/Face ID on iPhone and iPad and Fingerprint/Face/Iris/PIN on Android Phones.
|
||||
|
||||
Trusted device is a mode for the user to add a device that doesn't support security keys like iOS and andriod without fingerprints or NFC.
|
||||
Trusted device is a mode for the user to add a device that doesn't support security keys like Android without fingerprints or NFC.
|
||||
|
||||
**Note**: `U2F and FIDO2 can only be served under secure context (https)`
|
||||
|
||||
Package tested with Django 1.8, Django 2.1 on Python 2.7 and Python 3.5+ but it was not checked with any version in between but open for issues.
|
||||
Package tested with Django 1.8, Django 2.2 on Python 2.7 and Python 3.5+ but it was not checked with any version in between but open for issues.
|
||||
|
||||
Depends on
|
||||
|
||||
@@ -29,11 +37,23 @@ Depends on
|
||||
* ua-parser
|
||||
* user-agents
|
||||
* python-jose
|
||||
* fido2==0.7
|
||||
|
||||
* fido2==0.9.0
|
||||
|
||||
# Installation
|
||||
1. `pip install django-mfa2`
|
||||
1. using pip
|
||||
|
||||
`pip install django-mfa2`
|
||||
2. Using Conda forge
|
||||
|
||||
`conda config --add channels conda-forge`
|
||||
|
||||
`conda install django-mfa2`
|
||||
|
||||
For more info, see the conda-forge repo (https://github.com/conda-forge/django-mfa2-feedstock)
|
||||
|
||||
Thanks for [swainn](https://github.com/swainn) for adding package to conda-forge
|
||||
|
||||
# Usage
|
||||
1. in your settings.py add the application to your installed apps
|
||||
```python
|
||||
INSTALLED_APPS=(
|
||||
@@ -45,17 +65,22 @@ Depends on
|
||||
`python manage.py collectstatic`
|
||||
1. Add the following settings to your file
|
||||
|
||||
```python
|
||||
```python
|
||||
MFA_UNALLOWED_METHODS=() # Methods that shouldn't be allowed for the user
|
||||
MFA_LOGIN_CALLBACK="" # A function that should be called by username to login the user in session
|
||||
MFA_RECHECK=True # Allow random rechecking of the user
|
||||
MFA_REDIRECT_AFTER_REGISTRATION="mfa_home" # Allows Changing the page after successful registeration
|
||||
MFA_SUCCESS_REGISTRATION_MSG = "Go to Security Home" # The text of the link
|
||||
MFA_RECHECK_MIN=10 # Minimum interval in seconds
|
||||
MFA_RECHECK_MAX=30 # Maximum in seconds
|
||||
MFA_QUICKLOGIN=True # Allow quick login for returning users by provide only their 2FA
|
||||
MFA_HIDE_DISABLE=('FIDO2',) # Can the user disable his key (Added in 1.2.0).
|
||||
MFA_HIDE_DISABLE=('FIDO2',) # Can the user disable his key (Added in 1.2.0).
|
||||
MFA_OWNED_BY_ENTERPRISE = FALSE # Who owns security keys
|
||||
|
||||
TOKEN_ISSUER_NAME="PROJECT_NAME" #TOTP Issuer name
|
||||
|
||||
MFA_TOTP_FAILURE_LIMIT = 3 # Allowed TOTP Failures / user
|
||||
MFA_TOTP_FAILURE_WINDOW = 5 # The number of minutes to check failed logins against.
|
||||
|
||||
U2F_APPID="https://localhost" #URL For U2F
|
||||
FIDO_SERVER_ID=u"localehost" # Server rp id for FIDO2, it the full domain of your project
|
||||
FIDO_SERVER_NAME=u"PROJECT_NAME"
|
||||
@@ -67,41 +92,48 @@ Depends on
|
||||
* TOTP
|
||||
* Trusted_Devices
|
||||
* Email
|
||||
|
||||
**Note**: Starting version 1.1, ~~FIDO_LOGIN_URL~~ isn't required for FIDO2 anymore.
|
||||
|
||||
|
||||
**Notes**:
|
||||
* Starting version 1.1, ~~FIDO_LOGIN_URL~~ isn't required for FIDO2 anymore.
|
||||
* Starting version 1.7.0, Key owners can be specified.
|
||||
* Starting version 2.2.0
|
||||
* Added: `MFA_SUCCESS_REGISTRATION_MSG` & `MFA_REDIRECT_AFTER_REGISTRATION`
|
||||
* Starting version 2.3.0
|
||||
* Added: `MFA_TOTP_FAILURE_LIMIT` & `MFA_TOTP_FAILURE_WINDOW`
|
||||
1. Break your login function
|
||||
|
||||
Usually your login function will check for username and password, log the user in if the username and password are correct and create the user session, to support mfa, this has to change
|
||||
|
||||
|
||||
* authenticate the user
|
||||
* if username and password are correct , check if the user has mfa or not
|
||||
* if user has mfa then redirect to mfa page
|
||||
* if user doesn't have mfa then call your function to create the user session
|
||||
|
||||
```python
|
||||
def login(request): # this function handles the login form POST
|
||||
user = auth.authenticate(username=username, password=password)
|
||||
if user is not None: # if the user object exist
|
||||
from mfa.helpers import has_mfa
|
||||
res = has_mfa(username = username,request=request) # has_mfa returns false or HttpResponseRedirect
|
||||
from mfa.helpers import has_mfa
|
||||
|
||||
def login(request): # this function handles the login form POST
|
||||
user = auth.authenticate(username=username, password=password)
|
||||
if user is not None: # if the user object exist
|
||||
res = has_mfa(username=username, request=request) # has_mfa returns false or HttpResponseRedirect
|
||||
if res:
|
||||
return res
|
||||
return log_user_in(request,username=user.username)
|
||||
#log_user_in is a function that handles creatung user session, it should be in the setting file as MFA_CALLBACK
|
||||
return log_user_in(request, username=user.username)
|
||||
# log_user_in is a function that handles creating user session, it should be in the setting file as MFA_CALLBACK
|
||||
```
|
||||
1. Add mfa to urls.py
|
||||
```python
|
||||
```python
|
||||
import mfa
|
||||
import mfa.TrustedDevice
|
||||
urls_patterns= [
|
||||
'...',
|
||||
url(r'^mfa/', include('mfa.urls')),
|
||||
url(r'devices/add$', mfa.TrustedDevice.add,name="mfa_add_new_trusted_device"), # This short link to add new trusted device
|
||||
'....',
|
||||
]
|
||||
```
|
||||
1. Provide `mfa_auth_base.html` in your templaes with block called 'head' and 'content'
|
||||
|
||||
urls_patterns = [
|
||||
'...',
|
||||
url(r'^mfa/', include('mfa.urls')),
|
||||
url(r'devices/add$', mfa.TrustedDevice.add,name="mfa_add_new_trusted_device"), # This short link to add new trusted device
|
||||
'....',
|
||||
]
|
||||
```
|
||||
1. Provide `mfa_auth_base.html` in your templates with block called 'head' and 'content'
|
||||
The template will be included during the user login.
|
||||
If you will use Email Token method, then you have to provide template named `mfa_email_token_template.html` that will content the format of the email with parameter named `user` and `otp`.
|
||||
1. To match the look and feel of your project, MFA includes `base.html` but it needs blocks named `head` & `content` to added its content to it.
|
||||
@@ -114,39 +146,52 @@ For Example, See https://github.com/mkalioby/AutoDeploy/commit/5f1d94b1804e0aa33
|
||||
|
||||
To be able to go passwordless for returning users, create a cookie named 'base_username' containing username as shown in snippet below
|
||||
```python
|
||||
response = render(request, 'Dashboard.html', context))
|
||||
if request.session.get("mfa",{}).get("verified",False) and getattr(settings,"MFA_QUICKLOGIN",False):
|
||||
if request.session["mfa"]["method"]!="Trusted Device":
|
||||
response.set_cookie("base_username", request.user.username, path="/",max_age = 15*24*60*60)
|
||||
return response
|
||||
response = render(request, 'Dashboard.html', context))
|
||||
if request.session.get("mfa", {}).get("verified", False) and getattr(settings, "MFA_QUICKLOGIN", False):
|
||||
if request.session["mfa"]["method"] != "Trusted Device":
|
||||
response.set_cookie("base_username", request.user.username, path="/", max_age=15 * 24 * 60 * 60)
|
||||
return response
|
||||
```
|
||||
|
||||
Second, update the GET part of your login view
|
||||
```python
|
||||
if "mfa" in settings.INSTALLED_APPS and getattr(settings,"MFA_QUICKLOGIN",False) and request.COOKIES.get('base_username'):
|
||||
username=request.COOKIES.get('base_username')
|
||||
from mfa.helpers import has_mfa
|
||||
res = has_mfa(username = username,request=request,)
|
||||
if res: return res
|
||||
## continue and return the form.
|
||||
from mfa.helpers import has_mfa
|
||||
|
||||
if "mfa" in settings.INSTALLED_APPS and getattr(settings, "MFA_QUICKLOGIN", False) and request.COOKIES.get('base_username'):
|
||||
username=request.COOKIES.get('base_username')
|
||||
res = has_mfa(username=username, request=request)
|
||||
if res:
|
||||
return res
|
||||
# continue and return the form.
|
||||
```
|
||||
# Checking MFA on Client Side
|
||||
|
||||
Sometimes you like to verify that the user is still there so simple you can ask django-mfa2 to check that for you
|
||||
|
||||
```html
|
||||
{% include 'mfa_check.html' %}
|
||||
{% include 'mfa_check.html' %}
|
||||
```
|
||||
````js
|
||||
function success_func() {
|
||||
//logic if mfa check succeeds
|
||||
// logic if mfa check succeeds
|
||||
}
|
||||
function fail_func() {
|
||||
//logic if mfa check fails
|
||||
// logic if mfa check fails
|
||||
}
|
||||
function some_func() {
|
||||
recheck_mfa(success_func,fail_func,MUST_BE_MFA)
|
||||
//MUST_BE_MFA true or false, if the user must has with MFA
|
||||
}
|
||||
recheck_mfa(success_func, fail_func, MUST_BE_MFA)
|
||||
// MUST_BE_MFA true or false, if the user must has with MFA
|
||||
}
|
||||
|
||||
````
|
||||
|
||||
# Contributors
|
||||
* [mahmoodnasr](https://github.com/mahmoodnasr)
|
||||
* [d3cline](https://github.com/d3cline)
|
||||
* [swainn](https://github.com/swainn)
|
||||
* [unramk](https://github.com/unramk)
|
||||
* [willingham](https://github.com/willingham)
|
||||
|
||||
|
||||
# Security contact information
|
||||
To report a security vulnerability, please use the [Tidelift security contact](https://tidelift.com/security). Tidelift will coordinate the fix and disclosure.
|
||||
|
||||
+11
-11
@@ -3,21 +3,21 @@
|
||||
## Break your login function
|
||||
|
||||
Usually your login function will check for username and password, log the user in if the username and password are correct and create the user session, to support mfa, this has to change
|
||||
|
||||
|
||||
* authenticate the user
|
||||
* if username and password are correct , check if the user has mfa or not
|
||||
* if user has mfa then redirect to mfa page
|
||||
* if user doesn't have mfa then call your function to create the user session
|
||||
|
||||
<code>
|
||||
def login(request): # this function handles the login form POST
|
||||
user = auth.authenticate(username=username, password=password)
|
||||
if user is not None: # if the user object exist
|
||||
from mfa.helpers import has_mfa
|
||||
res = has_mfa(username = username,request=request) # has_mfa returns false or HttpResponseRedirect
|
||||
if res:
|
||||
return res
|
||||
return log_user_in(request,username=user.username)
|
||||
```python
|
||||
def login(request): # this function handles the login form POST
|
||||
user = auth.authenticate(username=username, password=password)
|
||||
if user is not None: # if the user object exist
|
||||
from mfa.helpers import has_mfa
|
||||
res = has_mfa(username = username,request=request) # has_mfa returns false or HttpResponseRedirect
|
||||
if res:
|
||||
return res
|
||||
return log_user_in(request,username=user.username)
|
||||
#log_user_in is a function that handles creatung user session, it should be in the setting file as MFA_CALLBACK
|
||||
</code>
|
||||
```
|
||||
|
||||
|
||||
@@ -1,5 +1,5 @@
|
||||
# Installation & Configuration
|
||||
1. Install the package
|
||||
1. Install the package
|
||||
```sh
|
||||
pip install django-mfa2
|
||||
```
|
||||
@@ -17,27 +17,27 @@
|
||||
MFA_RECHECK=True # Allow random rechecking of the user
|
||||
MFA_RECHECK_MIN=10 # Minimum interval in seconds
|
||||
MFA_RECHECK_MAX=30 # Maximum in seconds
|
||||
MFA_QUICKLOGIN=True # Allow quick login for returning users by provide only their 2FA
|
||||
|
||||
MFA_QUICKLOGIN=True # Allow quick login for returning users by provide only their 2FA
|
||||
|
||||
TOKEN_ISSUER_NAME="PROJECT_NAME" #TOTP Issuer name
|
||||
|
||||
|
||||
U2F_APPID="https://localhost" #URL For U2
|
||||
FIDO_SERVER_ID=u"localehost" # Server rp id for FIDO2, it the full domain of your project
|
||||
FIDO_SERVER_NAME=u"PROJECT_NAME"
|
||||
FIDO_LOGIN_URL=BASE_URL
|
||||
```
|
||||
|
||||
|
||||
**Method Names**
|
||||
* U2F
|
||||
* FIDO2
|
||||
* TOTP
|
||||
* Trusted_Devices
|
||||
* Email
|
||||
|
||||
|
||||
**Note**: Starting version 1.1, ~~FIDO_LOGIN_URL~~ isn't required for FIDO2 anymore.
|
||||
|
||||
|
||||
1. Add mfa to urls.py
|
||||
|
||||
|
||||
```python
|
||||
import mfa
|
||||
import mfa.TrustedDevice
|
||||
@@ -48,7 +48,7 @@
|
||||
'....',
|
||||
]
|
||||
```
|
||||
1. Provide `mfa_auth_base.html` in your templaes with block called 'head' and 'content'
|
||||
1. Provide `mfa_auth_base.html` in your templates with block called 'head' and 'content'
|
||||
The template will be included during the user login.
|
||||
If you will use Email Token method, then you have to provide template named `mfa_email_token_template.html` that will content the format of the email with parameter named `user` and `otp`.
|
||||
1. To match the look and feel of your project, MFA includes `base.html` but it needs blocks named `head` & `content` to added its content to it.
|
||||
|
||||
+24
-18
@@ -1,30 +1,36 @@
|
||||
from django.shortcuts import render
|
||||
from django.http import HttpResponseRedirect
|
||||
from django.urls import reverse
|
||||
from django.contrib.auth import authenticate,login,logout
|
||||
from django.contrib.auth import authenticate, login, logout
|
||||
from django.contrib.auth.models import User
|
||||
from django.http import HttpResponseRedirect
|
||||
from django.shortcuts import render
|
||||
from django.urls import reverse
|
||||
|
||||
from mfa.helpers import has_mfa
|
||||
|
||||
|
||||
def loginView(request):
|
||||
context={}
|
||||
if request.method=="POST":
|
||||
username=request.POST["username"]
|
||||
password=request.POST["password"]
|
||||
user=authenticate(username=username,password=password)
|
||||
context = {}
|
||||
if request.method == "POST":
|
||||
username = request.POST["username"]
|
||||
password = request.POST["password"]
|
||||
user = authenticate(username=username, password=password)
|
||||
if user:
|
||||
from mfa.helpers import has_mfa
|
||||
res = has_mfa(username = username, request = request) # has_mfa returns false or HttpResponseRedirect
|
||||
res = has_mfa(
|
||||
username=username, request=request
|
||||
) # has_mfa returns false or HttpResponseRedirect
|
||||
if res:
|
||||
return res
|
||||
return create_session(request,user.username)
|
||||
context["invalid"]=True
|
||||
return create_session(request, user.username)
|
||||
context["invalid"] = True
|
||||
return render(request, "login.html", context)
|
||||
|
||||
def create_session(request,username):
|
||||
user=User.objects.get(username=username)
|
||||
user.backend='django.contrib.auth.backends.ModelBackend'
|
||||
|
||||
def create_session(request, username):
|
||||
user = User.objects.get(username=username)
|
||||
user.backend = "django.contrib.auth.backends.ModelBackend"
|
||||
login(request, user)
|
||||
return HttpResponseRedirect(reverse('home'))
|
||||
return HttpResponseRedirect(reverse("home"))
|
||||
|
||||
|
||||
def logoutView(request):
|
||||
logout(request)
|
||||
return render(request,"logout.html",{})
|
||||
return render(request, "logout.html", {})
|
||||
|
||||
+71
-68
@@ -20,7 +20,7 @@ BASE_DIR = os.path.dirname(os.path.dirname(os.path.abspath(__file__)))
|
||||
# See https://docs.djangoproject.com/en/2.0/howto/deployment/checklist/
|
||||
|
||||
# SECURITY WARNING: keep the secret key used in production secret!
|
||||
SECRET_KEY = '#9)q!_i3@pr-^3oda(e^3$x!kq3b4f33#5l@+=+&vuz+p6gb3g'
|
||||
SECRET_KEY = "#9)q!_i3@pr-^3oda(e^3$x!kq3b4f33#5l@+=+&vuz+p6gb3g"
|
||||
|
||||
# SECURITY WARNING: don't run with debug turned on in production!
|
||||
DEBUG = True
|
||||
@@ -31,54 +31,54 @@ ALLOWED_HOSTS = []
|
||||
# Application definition
|
||||
|
||||
INSTALLED_APPS = [
|
||||
'django.contrib.admin',
|
||||
'django.contrib.auth',
|
||||
'django.contrib.contenttypes',
|
||||
'django.contrib.sessions',
|
||||
'django.contrib.messages',
|
||||
'django.contrib.staticfiles',
|
||||
'mfa',
|
||||
'sslserver'
|
||||
"django.contrib.admin",
|
||||
"django.contrib.auth",
|
||||
"django.contrib.contenttypes",
|
||||
"django.contrib.sessions",
|
||||
"django.contrib.messages",
|
||||
"django.contrib.staticfiles",
|
||||
"mfa",
|
||||
"sslserver",
|
||||
]
|
||||
|
||||
MIDDLEWARE = [
|
||||
'django.middleware.security.SecurityMiddleware',
|
||||
'django.contrib.sessions.middleware.SessionMiddleware',
|
||||
'django.middleware.common.CommonMiddleware',
|
||||
'django.middleware.csrf.CsrfViewMiddleware',
|
||||
'django.contrib.auth.middleware.AuthenticationMiddleware',
|
||||
'django.contrib.messages.middleware.MessageMiddleware',
|
||||
'django.middleware.clickjacking.XFrameOptionsMiddleware',
|
||||
"django.middleware.security.SecurityMiddleware",
|
||||
"django.contrib.sessions.middleware.SessionMiddleware",
|
||||
"django.middleware.common.CommonMiddleware",
|
||||
"django.middleware.csrf.CsrfViewMiddleware",
|
||||
"django.contrib.auth.middleware.AuthenticationMiddleware",
|
||||
"django.contrib.messages.middleware.MessageMiddleware",
|
||||
"django.middleware.clickjacking.XFrameOptionsMiddleware",
|
||||
]
|
||||
|
||||
ROOT_URLCONF = 'example.urls'
|
||||
ROOT_URLCONF = "example.urls"
|
||||
|
||||
TEMPLATES = [
|
||||
{
|
||||
'BACKEND': 'django.template.backends.django.DjangoTemplates',
|
||||
'DIRS': [os.path.join(BASE_DIR ,'example','templates' )],
|
||||
'APP_DIRS': True,
|
||||
'OPTIONS': {
|
||||
'context_processors': [
|
||||
'django.template.context_processors.debug',
|
||||
'django.template.context_processors.request',
|
||||
'django.contrib.auth.context_processors.auth',
|
||||
'django.contrib.messages.context_processors.messages',
|
||||
"BACKEND": "django.template.backends.django.DjangoTemplates",
|
||||
"DIRS": [os.path.join(BASE_DIR, "example", "templates")],
|
||||
"APP_DIRS": True,
|
||||
"OPTIONS": {
|
||||
"context_processors": [
|
||||
"django.template.context_processors.debug",
|
||||
"django.template.context_processors.request",
|
||||
"django.contrib.auth.context_processors.auth",
|
||||
"django.contrib.messages.context_processors.messages",
|
||||
],
|
||||
},
|
||||
},
|
||||
]
|
||||
|
||||
WSGI_APPLICATION = 'example.wsgi.application'
|
||||
WSGI_APPLICATION = "example.wsgi.application"
|
||||
|
||||
|
||||
# Database
|
||||
# https://docs.djangoproject.com/en/2.0/ref/settings/#databases
|
||||
|
||||
DATABASES = {
|
||||
'default': {
|
||||
'ENGINE': 'django.db.backends.sqlite3',
|
||||
'NAME': os.path.join(BASE_DIR, 'db.sqlite3'),
|
||||
"default": {
|
||||
"ENGINE": "django.db.backends.sqlite3",
|
||||
"NAME": "test_db",
|
||||
}
|
||||
}
|
||||
|
||||
@@ -86,28 +86,28 @@ DATABASES = {
|
||||
# Password validation
|
||||
# https://docs.djangoproject.com/en/2.0/ref/settings/#auth-password-validators
|
||||
|
||||
AUTH_PASSWORD_VALIDATORS = [
|
||||
{
|
||||
'NAME': 'django.contrib.auth.password_validation.UserAttributeSimilarityValidator',
|
||||
},
|
||||
{
|
||||
'NAME': 'django.contrib.auth.password_validation.MinimumLengthValidator',
|
||||
},
|
||||
{
|
||||
'NAME': 'django.contrib.auth.password_validation.CommonPasswordValidator',
|
||||
},
|
||||
{
|
||||
'NAME': 'django.contrib.auth.password_validation.NumericPasswordValidator',
|
||||
},
|
||||
]
|
||||
# AUTH_PASSWORD_VALIDATORS = [
|
||||
# {
|
||||
# "NAME": "django.contrib.auth.password_validation.UserAttributeSimilarityValidator",
|
||||
# },
|
||||
# {
|
||||
# "NAME": "django.contrib.auth.password_validation.MinimumLengthValidator",
|
||||
# },
|
||||
# {
|
||||
# "NAME": "django.contrib.auth.password_validation.CommonPasswordValidator",
|
||||
# },
|
||||
# {
|
||||
# "NAME": "django.contrib.auth.password_validation.NumericPasswordValidator",
|
||||
# },
|
||||
# ]
|
||||
|
||||
|
||||
# Internationalization
|
||||
# https://docs.djangoproject.com/en/2.0/topics/i18n/
|
||||
|
||||
LANGUAGE_CODE = 'en-us'
|
||||
LANGUAGE_CODE = "en-us"
|
||||
|
||||
TIME_ZONE = 'UTC'
|
||||
TIME_ZONE = "UTC"
|
||||
|
||||
USE_I18N = True
|
||||
|
||||
@@ -119,30 +119,33 @@ USE_TZ = True
|
||||
# Static files (CSS, JavaScript, Images)
|
||||
# https://docs.djangoproject.com/en/2.0/howto/static-files/
|
||||
|
||||
STATIC_URL = '/static/'
|
||||
#STATIC_ROOT=(os.path.join(BASE_DIR,'static'))
|
||||
STATICFILES_DIRS=[os.path.join(BASE_DIR,'static')]
|
||||
LOGIN_URL="/auth/login"
|
||||
STATIC_URL = "/static/"
|
||||
# STATIC_ROOT=(os.path.join(BASE_DIR,'static'))
|
||||
STATICFILES_DIRS = [os.path.join(BASE_DIR, "static")]
|
||||
LOGIN_URL = "/auth/login"
|
||||
|
||||
EMAIL_FROM='Test App'
|
||||
EMAIL_HOST="smtp.gmail.com"
|
||||
EMAIL_PORT=587
|
||||
EMAIL_HOST_USER="mkalioby@gmail.com"
|
||||
EMAIL_HOST_PASSWORD='wanted85'
|
||||
EMAIL_USE_TLS=True
|
||||
EMAIL_FROM = "Test App"
|
||||
EMAIL_HOST = "smtp.gmail.com"
|
||||
EMAIL_PORT = 587
|
||||
EMAIL_HOST_USER = ""
|
||||
EMAIL_HOST_PASSWORD = ""
|
||||
EMAIL_USE_TLS = True
|
||||
|
||||
|
||||
MFA_UNALLOWED_METHODS = () # Methods that shouldn't be allowed for the user
|
||||
MFA_LOGIN_CALLBACK = "example.auth.create_session" # A function that should be called by username to login the user in session
|
||||
MFA_RECHECK = True # Allow random rechecking of the user
|
||||
MFA_RECHECK_MIN = 10 # Minimum interval in seconds
|
||||
MFA_RECHECK_MAX = 30 # Maximum in seconds
|
||||
MFA_QUICKLOGIN = True # Allow quick login for returning users by provide only their 2FA
|
||||
MFA_HIDE_DISABLE = ("",) # Can the user disable his key (Added in 1.2.0).
|
||||
MFA_REDIRECT_AFTER_REGISTRATION = "registered"
|
||||
MFA_SUCCESS_REGISTRATION_MSG = "Go to Home"
|
||||
|
||||
MFA_UNALLOWED_METHODS=() # Methods that shouldn't be allowed for the user
|
||||
MFA_LOGIN_CALLBACK="example.auth.create_session" # A function that should be called by username to login the user in session
|
||||
MFA_RECHECK=True # Allow random rechecking of the user
|
||||
MFA_RECHECK_MIN=10 # Minimum interval in seconds
|
||||
MFA_RECHECK_MAX=30 # Maximum in seconds
|
||||
MFA_QUICKLOGIN=True # Allow quick login for returning users by provide only their 2FA
|
||||
MFA_HIDE_DISABLE=('FIDO2',) # Can the user disable his key (Added in 1.2.0).
|
||||
TOKEN_ISSUER_NAME = "PROJECT_NAME" # TOTP Issuer name
|
||||
|
||||
TOKEN_ISSUER_NAME="PROJECT_NAME" #TOTP Issuer name
|
||||
|
||||
U2F_APPID="https://localhost" #URL For U2F
|
||||
FIDO_SERVER_ID=u"localhost" # Server rp id for FIDO2, it the full domain of your project
|
||||
FIDO_SERVER_NAME=u"PROJECT_NAME"
|
||||
U2F_APPID = "https://localhost" # URL For U2F
|
||||
FIDO_SERVER_ID = (
|
||||
u"localhost" # Server rp id for FIDO2, it the full domain of your project
|
||||
)
|
||||
FIDO_SERVER_NAME = u"PROJECT_NAME"
|
||||
|
||||
@@ -12,6 +12,9 @@
|
||||
</ol>
|
||||
|
||||
<!-- Page Content -->
|
||||
{% if registered %}
|
||||
<div class="alert alert-success">Registered Successfully</div>
|
||||
{% endif %}
|
||||
<h1>Welcome {{ request.user.username }}!</h1>
|
||||
<hr>
|
||||
|
||||
|
||||
+10
-8
@@ -14,13 +14,15 @@ Including another URLconf
|
||||
2. Add a URL to urlpatterns: path('blog/', include('blog.urls'))
|
||||
"""
|
||||
from django.contrib import admin
|
||||
from django.urls import path,re_path,include
|
||||
from . import views,auth
|
||||
urlpatterns = [
|
||||
path('admin/', admin.site.urls),
|
||||
path('mfa/', include('mfa.urls')),
|
||||
path('auth/login',auth.loginView,name="login"),
|
||||
path('auth/logout',auth.logoutView,name="logout"),
|
||||
from django.urls import include, path
|
||||
|
||||
re_path('^$',views.home,name='home')
|
||||
from . import auth, views
|
||||
|
||||
urlpatterns = [
|
||||
path("admin/", admin.site.urls),
|
||||
path("mfa/", include("mfa.urls")),
|
||||
path("auth/login/", auth.loginView, name="login"),
|
||||
path("auth/logout/", auth.logoutView, name="logout"),
|
||||
path("", views.home, name="home"),
|
||||
path("registered/", views.registered, name="registered"),
|
||||
]
|
||||
|
||||
@@ -1,7 +1,12 @@
|
||||
from django.shortcuts import render
|
||||
from django.contrib.auth.decorators import login_required
|
||||
from django.shortcuts import render
|
||||
|
||||
|
||||
@login_required()
|
||||
def home(request):
|
||||
return render(request,"home.html",{})
|
||||
return render(request, "home.html", {})
|
||||
|
||||
|
||||
@login_required()
|
||||
def registered(request):
|
||||
return render(request, "home.html", {"registered": True})
|
||||
|
||||
@@ -1,2 +1,2 @@
|
||||
django==2.0
|
||||
django-sslserver
|
||||
django >= 2.2
|
||||
django_ssl
|
||||
|
||||
+18
-4
@@ -1,8 +1,22 @@
|
||||
from django.conf import settings
|
||||
from django.core.mail import EmailMessage
|
||||
from django.urls import reverse
|
||||
|
||||
def send(to,subject,body):
|
||||
From = "%s <%s>" % (settings.EMAIL_FROM, settings.EMAIL_HOST_USER)
|
||||
email = EmailMessage(subject,body,From,to)
|
||||
|
||||
def send(to, subject, body):
|
||||
from_email_address = settings.EMAIL_HOST_USER
|
||||
if "@" not in from_email_address:
|
||||
from_email_address = settings.DEFAULT_FROM_EMAIL
|
||||
From = "%s <%s>" % (settings.EMAIL_FROM, from_email_address)
|
||||
email = EmailMessage(subject, body, From, to)
|
||||
email.content_subtype = "html"
|
||||
return email.send(False)
|
||||
return email.send(False)
|
||||
|
||||
|
||||
def get_redirect_url():
|
||||
return {
|
||||
"redirect_html": reverse(
|
||||
getattr(settings, "MFA_REDIRECT_AFTER_REGISTRATION", "mfa_home")
|
||||
),
|
||||
"reg_success_msg": getattr(settings, "MFA_SUCCESS_REGISTRATION_MSG"),
|
||||
}
|
||||
|
||||
+67
-36
@@ -1,59 +1,90 @@
|
||||
import datetime
|
||||
import random
|
||||
from random import randint
|
||||
|
||||
from django.conf import settings
|
||||
from django.contrib.auth import get_user_model
|
||||
from django.http import HttpResponseRedirect
|
||||
from django.shortcuts import render
|
||||
from django.template.context_processors import csrf
|
||||
import datetime,random
|
||||
from random import randint
|
||||
from .models import *
|
||||
#from django.template.context import RequestContext
|
||||
from .views import login
|
||||
from django.urls import reverse
|
||||
from django.utils import timezone
|
||||
from django.views.decorators.cache import never_cache
|
||||
|
||||
from .Common import send
|
||||
def sendEmail(request,username,secret):
|
||||
from django.contrib.auth import get_user_model
|
||||
from .models import UserKey
|
||||
from .views import login
|
||||
|
||||
|
||||
def send_email(request, username, secret):
|
||||
"""Send Email to the user after rendering `mfa_email_token_template`"""
|
||||
User = get_user_model()
|
||||
key = getattr(User, 'USERNAME_FIELD', 'username')
|
||||
key = getattr(User, "USERNAME_FIELD", "username")
|
||||
kwargs = {key: username}
|
||||
user = User.objects.get(**kwargs)
|
||||
res=render(request,"mfa_email_token_template.html",{"request":request,"user":user,'otp':secret})
|
||||
return send([user.email],"OTP", str(res.content))
|
||||
res = render(
|
||||
request,
|
||||
"mfa_email_token_template.html",
|
||||
{"request": request, "user": user, "otp": secret},
|
||||
)
|
||||
return send([user.email], "OTP", res.content.decode())
|
||||
|
||||
|
||||
@never_cache
|
||||
def start(request):
|
||||
"""Start adding email as a 2nd factor"""
|
||||
context = csrf(request)
|
||||
if request.method == "POST":
|
||||
if request.session["email_secret"] == request.POST["otp"]:
|
||||
uk=User_Keys()
|
||||
uk.username=request.user.username
|
||||
uk.key_type="Email"
|
||||
uk.enabled=1
|
||||
if request.session["email_secret"] == request.POST["otp"]: # if successful
|
||||
uk = UserKey()
|
||||
uk.username = request.user.username
|
||||
uk.key_type = "Email"
|
||||
uk.enabled = 1
|
||||
uk.save()
|
||||
from django.http import HttpResponseRedirect
|
||||
try:
|
||||
from django.core.urlresolvers import reverse
|
||||
except:
|
||||
from django.urls import reverse
|
||||
return HttpResponseRedirect(reverse('mfa_home'))
|
||||
return HttpResponseRedirect(
|
||||
reverse(
|
||||
getattr(settings, "MFA_REDIRECT_AFTER_REGISTRATION", "mfa_home")
|
||||
)
|
||||
)
|
||||
context["invalid"] = True
|
||||
else:
|
||||
request.session["email_secret"] = str(randint(0,100000))
|
||||
if sendEmail(request, request.user.username, request.session["email_secret"]):
|
||||
request.session["email_secret"] = str(
|
||||
randint(0, 100000)
|
||||
) # generate a random integer
|
||||
if send_email(request, request.user.username, request.session["email_secret"]):
|
||||
context["sent"] = True
|
||||
return render(request,"Email/Add.html", context)
|
||||
return render(request, "Email/Add.html", context)
|
||||
|
||||
|
||||
@never_cache
|
||||
def auth(request):
|
||||
context=csrf(request)
|
||||
if request.method=="POST":
|
||||
if request.session["email_secret"]==request.POST["otp"].strip():
|
||||
uk = User_Keys.objects.get(username=request.session["base_username"], key_type="Email")
|
||||
mfa = {"verified": True, "method": "Email","id":uk.id}
|
||||
"""Authenticating the user by email."""
|
||||
context = csrf(request)
|
||||
if request.method == "POST":
|
||||
if request.session["email_secret"] == request.POST["otp"].strip():
|
||||
uk = UserKey.objects.get(
|
||||
username=request.session["base_username"], key_type="Email"
|
||||
)
|
||||
mfa = {"verified": True, "method": "Email", "id": uk.id}
|
||||
if getattr(settings, "MFA_RECHECK", False):
|
||||
mfa["next_check"] = int((datetime.datetime.now() + datetime.timedelta(
|
||||
seconds = random.randint(settings.MFA_RECHECK_MIN, settings.MFA_RECHECK_MAX))).strftime("%s"))
|
||||
mfa["next_check"] = datetime.datetime.timestamp(
|
||||
datetime.datetime.now()
|
||||
+ datetime.timedelta(
|
||||
seconds=random.randint(
|
||||
settings.MFA_RECHECK_MIN, settings.MFA_RECHECK_MAX
|
||||
)
|
||||
)
|
||||
)
|
||||
request.session["mfa"] = mfa
|
||||
|
||||
from django.utils import timezone
|
||||
uk.last_used=timezone.now()
|
||||
uk.last_used = timezone.now()
|
||||
uk.save()
|
||||
return login(request)
|
||||
context["invalid"]=True
|
||||
context["invalid"] = True
|
||||
else:
|
||||
request.session["email_secret"] = str(randint(0, 100000))
|
||||
if sendEmail(request, request.session["base_username"], request.session["email_secret"]):
|
||||
if send_email(
|
||||
request, request.session["base_username"], request.session["email_secret"]
|
||||
):
|
||||
context["sent"] = True
|
||||
return render(request,"Email/Auth.html", context)
|
||||
return render(request, "Email/Auth.html", context)
|
||||
|
||||
+154
-84
@@ -1,117 +1,187 @@
|
||||
from fido2.client import ClientData
|
||||
from fido2.server import Fido2Server, RelyingParty
|
||||
from fido2.ctap2 import AttestationObject, AuthenticatorData
|
||||
from django.template.context_processors import csrf
|
||||
from django.views.decorators.csrf import csrf_exempt
|
||||
from django.shortcuts import render
|
||||
#from django.template.context import RequestContext
|
||||
import simplejson
|
||||
from fido2 import cbor
|
||||
from django.http import HttpResponse
|
||||
from django.conf import settings
|
||||
from .models import *
|
||||
from fido2.utils import websafe_decode,websafe_encode
|
||||
from fido2.ctap2 import AttestedCredentialData
|
||||
from .views import login
|
||||
import datetime
|
||||
import random
|
||||
import time
|
||||
import traceback
|
||||
|
||||
from django.conf import settings
|
||||
from django.http import HttpResponse, JsonResponse
|
||||
from django.shortcuts import render
|
||||
from django.template.context_processors import csrf
|
||||
from django.utils import timezone
|
||||
from django.views.decorators.csrf import csrf_exempt
|
||||
from fido2 import cbor
|
||||
from fido2.client import ClientData
|
||||
from fido2.ctap2 import AttestationObject, AttestedCredentialData, AuthenticatorData
|
||||
from fido2.server import Fido2Server, PublicKeyCredentialRpEntity
|
||||
from fido2.utils import websafe_decode, websafe_encode
|
||||
|
||||
from .Common import get_redirect_url
|
||||
from .models import UserKey
|
||||
from .views import login, reset_cookie
|
||||
|
||||
|
||||
def recheck(request):
|
||||
"""Starts FIDO2 recheck"""
|
||||
context = csrf(request)
|
||||
context["mode"]="recheck"
|
||||
return request("FIDO2/recheck.html", context)
|
||||
context["mode"] = "recheck"
|
||||
request.session["mfa_recheck"] = True
|
||||
return render(request, "FIDO2/recheck.html", context)
|
||||
|
||||
|
||||
def getServer():
|
||||
rp = RelyingParty(settings.FIDO_SERVER_ID, settings.FIDO_SERVER_NAME)
|
||||
def get_server():
|
||||
"""Get Server Info from settings and returns a Fido2Server"""
|
||||
rp = PublicKeyCredentialRpEntity(settings.FIDO_SERVER_ID, settings.FIDO_SERVER_NAME)
|
||||
return Fido2Server(rp)
|
||||
def begin_registeration(request):
|
||||
server = getServer()
|
||||
registration_data, state = server.register_begin({
|
||||
u'id': request.user.username.encode("utf8"),
|
||||
u'name': (request.user.first_name + " " + request.user.last_name),
|
||||
u'displayName': request.user.username,
|
||||
}, getUserCredentials(request.user.username))
|
||||
request.session['fido_state'] = state
|
||||
|
||||
return HttpResponse(cbor.encode(registration_data),content_type='application/octet-stream')
|
||||
|
||||
def begin_registeration(request):
|
||||
"""Starts registering a new FIDO Device, called from API"""
|
||||
server = get_server()
|
||||
registration_data, state = server.register_begin(
|
||||
{
|
||||
u"id": request.user.username.encode("utf8"),
|
||||
u"name": (request.user.first_name + " " + request.user.last_name),
|
||||
u"displayName": request.user.username,
|
||||
},
|
||||
get_user_credentials(request.user.username),
|
||||
)
|
||||
request.session["fido_state"] = state
|
||||
|
||||
return HttpResponse(
|
||||
cbor.encode(registration_data), content_type="application/octet-stream"
|
||||
)
|
||||
|
||||
|
||||
@csrf_exempt
|
||||
def complete_reg(request):
|
||||
"""Completes the registeration, called by API"""
|
||||
try:
|
||||
data = cbor.decode(request.body)
|
||||
|
||||
client_data = ClientData(data['clientDataJSON'])
|
||||
att_obj = AttestationObject((data['attestationObject']))
|
||||
server = getServer()
|
||||
client_data = ClientData(data["clientDataJSON"])
|
||||
att_obj = AttestationObject((data["attestationObject"]))
|
||||
server = get_server()
|
||||
auth_data = server.register_complete(
|
||||
request.session['fido_state'],
|
||||
client_data,
|
||||
att_obj
|
||||
request.session["fido_state"], client_data, att_obj
|
||||
)
|
||||
encoded = websafe_encode(auth_data.credential_data)
|
||||
uk=User_Keys()
|
||||
uk = UserKey()
|
||||
uk.username = request.user.username
|
||||
uk.properties = {"device":encoded,"type":att_obj.fmt,}
|
||||
uk.properties = {
|
||||
"device": encoded,
|
||||
"type": att_obj.fmt,
|
||||
}
|
||||
uk.owned_by_enterprise = getattr(settings, "MFA_OWNED_BY_ENTERPRISE", False)
|
||||
uk.key_type = "FIDO2"
|
||||
uk.save()
|
||||
return HttpResponse(simplejson.dumps({'status': 'OK'}))
|
||||
return JsonResponse({"status": "OK"})
|
||||
except Exception as exp:
|
||||
from raven.contrib.django.raven_compat.models import client
|
||||
import traceback
|
||||
client.captureException()
|
||||
return HttpResponse(simplejson.dumps({'status': 'ERR',"message":"Error on server, please try again later"}))
|
||||
def start(request):
|
||||
context = csrf(request)
|
||||
return render(request,"FIDO2/Add.html", context)
|
||||
print(traceback.format_exc())
|
||||
return JsonResponse(
|
||||
{"status": "ERR", "message": "Error on server, please try again later"}
|
||||
)
|
||||
|
||||
def getUserCredentials(username):
|
||||
|
||||
def start(request):
|
||||
"""Start Registeration a new FIDO Token"""
|
||||
context = csrf(request)
|
||||
context.update(get_redirect_url())
|
||||
return render(request, "FIDO2/Add.html", context)
|
||||
|
||||
|
||||
def get_user_credentials(username):
|
||||
credentials = []
|
||||
for uk in User_Keys.objects.filter(username = username, key_type = "FIDO2"):
|
||||
credentials.append(AttestedCredentialData(websafe_decode(uk.properties["device"])))
|
||||
for uk in UserKey.objects.filter(username=username, key_type="FIDO2"):
|
||||
credentials.append(
|
||||
AttestedCredentialData(websafe_decode(uk.properties["device"]))
|
||||
)
|
||||
return credentials
|
||||
|
||||
|
||||
def auth(request):
|
||||
context=csrf(request)
|
||||
return render(request,"FIDO2/Auth.html",context)
|
||||
context = csrf(request)
|
||||
return render(request, "FIDO2/Auth.html", context)
|
||||
|
||||
|
||||
def authenticate_begin(request):
|
||||
server = getServer()
|
||||
credentials=getUserCredentials(request.session.get("base_username",request.user.username))
|
||||
server = get_server()
|
||||
credentials = get_user_credentials(
|
||||
request.session.get("base_username", request.user.username)
|
||||
)
|
||||
auth_data, state = server.authenticate_begin(credentials)
|
||||
request.session['fido_state'] = state
|
||||
return HttpResponse(cbor.encode(auth_data),content_type="application/octet-stream")
|
||||
request.session["fido_state"] = state
|
||||
return HttpResponse(cbor.encode(auth_data), content_type="application/octet-stream")
|
||||
|
||||
|
||||
@csrf_exempt
|
||||
def authenticate_complete(request):
|
||||
credentials = []
|
||||
username=request.session.get("base_username",request.user.username)
|
||||
server=getServer()
|
||||
credentials=getUserCredentials(username)
|
||||
data = cbor.decode(request.body)
|
||||
credential_id = data['credentialId']
|
||||
client_data = ClientData(data['clientDataJSON'])
|
||||
auth_data = AuthenticatorData(data['authenticatorData'])
|
||||
signature = data['signature']
|
||||
try:
|
||||
credentials = []
|
||||
username = request.session.get("base_username", request.user.username)
|
||||
server = get_server()
|
||||
credentials = get_user_credentials(username)
|
||||
data = cbor.decode(request.body)
|
||||
credential_id = data["credentialId"]
|
||||
client_data = ClientData(data["clientDataJSON"])
|
||||
auth_data = AuthenticatorData(data["authenticatorData"])
|
||||
signature = data["signature"]
|
||||
try:
|
||||
cred = server.authenticate_complete(
|
||||
request.session.pop("fido_state"),
|
||||
credentials,
|
||||
credential_id,
|
||||
client_data,
|
||||
auth_data,
|
||||
signature,
|
||||
)
|
||||
except ValueError:
|
||||
return JsonResponse(
|
||||
{
|
||||
"status": "ERR",
|
||||
"message": "Wrong challenge received, make sure that this is your security and try again.",
|
||||
}
|
||||
)
|
||||
except Exception as excep:
|
||||
print(traceback.format_exc())
|
||||
return JsonResponse({"status": "ERR", "message": excep.message})
|
||||
|
||||
cred = server.authenticate_complete(
|
||||
request.session.pop('fido_state'),
|
||||
credentials,
|
||||
credential_id,
|
||||
client_data,
|
||||
auth_data,
|
||||
signature
|
||||
)
|
||||
keys = User_Keys.objects.filter(username=username, key_type="FIDO2",enabled=1)
|
||||
import random
|
||||
for k in keys:
|
||||
if AttestedCredentialData(websafe_decode(k.properties["device"])).credential_id == cred.credential_id:
|
||||
k.last_used = timezone.now()
|
||||
k.save()
|
||||
mfa = {"verified": True, "method": "FIDO2",'id':k.id}
|
||||
if getattr(settings, "MFA_RECHECK", False):
|
||||
mfa["next_check"] = int((datetime.datetime.now()+ datetime.timedelta(
|
||||
seconds=random.randint(settings.MFA_RECHECK_MIN, settings.MFA_RECHECK_MAX))).strftime("%s"))
|
||||
request.session["mfa"] = mfa
|
||||
res=login(request)
|
||||
return HttpResponse(simplejson.dumps({'status':"OK","redirect":res["location"]}),content_type="application/json")
|
||||
return HttpResponse(simplejson.dumps({'status': "err"}),content_type="application/json")
|
||||
if request.session.get("mfa_recheck", False):
|
||||
request.session["mfa"]["rechecked_at"] = time.time()
|
||||
return JsonResponse({"status": "OK"})
|
||||
else:
|
||||
keys = UserKey.objects.filter(
|
||||
username=username, key_type="FIDO2", enabled=1
|
||||
)
|
||||
for k in keys:
|
||||
if (
|
||||
AttestedCredentialData(
|
||||
websafe_decode(k.properties["device"])
|
||||
).credential_id
|
||||
== cred.credential_id
|
||||
):
|
||||
k.last_used = timezone.now()
|
||||
k.save()
|
||||
mfa = {"verified": True, "method": "FIDO2", "id": k.id}
|
||||
if getattr(settings, "MFA_RECHECK", False):
|
||||
mfa["next_check"] = datetime.datetime.timestamp(
|
||||
(
|
||||
datetime.datetime.now()
|
||||
+ datetime.timedelta(
|
||||
seconds=random.randint(
|
||||
settings.MFA_RECHECK_MIN,
|
||||
settings.MFA_RECHECK_MAX,
|
||||
)
|
||||
)
|
||||
)
|
||||
)
|
||||
request.session["mfa"] = mfa
|
||||
if not request.user.is_authenticated:
|
||||
res = login(request)
|
||||
if "location" not in res:
|
||||
return reset_cookie(request)
|
||||
return JsonResponse(
|
||||
{"status": "OK", "redirect": res["location"]}
|
||||
)
|
||||
return JsonResponse({"status": "OK"})
|
||||
except Exception as exp:
|
||||
return JsonResponse({"status": "ERR", "message": str(exp)})
|
||||
|
||||
+101
-73
@@ -1,134 +1,162 @@
|
||||
import string
|
||||
import random
|
||||
from django.shortcuts import render
|
||||
from django.http import HttpResponse
|
||||
from django.template.context import RequestContext
|
||||
from django.template.context_processors import csrf
|
||||
from .models import *
|
||||
import string
|
||||
from datetime import datetime, timedelta
|
||||
|
||||
import user_agents
|
||||
from django.conf import settings
|
||||
from django.http import HttpResponse
|
||||
from django.shortcuts import render
|
||||
from django.template.context_processors import csrf
|
||||
from django.utils import timezone
|
||||
from jose import jwt
|
||||
|
||||
from .Common import send
|
||||
from .models import UserKey
|
||||
|
||||
|
||||
def id_generator(size=6, chars=string.ascii_uppercase + string.digits):
|
||||
x=''.join(random.choice(chars) for _ in range(size))
|
||||
if not User_Keys.objects.filter(properties__shas="$.key="+x).exists(): return x
|
||||
else: return id_generator(size,chars)
|
||||
x = "".join(random.choice(chars) for _ in range(size))
|
||||
if not UserKey.objects.filter(properties__shas="$.key=" + x).exists():
|
||||
return x
|
||||
else:
|
||||
return id_generator(size, chars)
|
||||
|
||||
def getUserAgent(request):
|
||||
id=id=request.session.get("td_id",None)
|
||||
|
||||
def get_user_agent(request):
|
||||
id = id = request.session.get("td_id", None)
|
||||
if id:
|
||||
tk=User_Keys.objects.get(id=id)
|
||||
if tk.properties.get("user_agent","")!="":
|
||||
tk = UserKey.objects.get(id=id)
|
||||
if tk.properties.get("user_agent", "") != "":
|
||||
ua = user_agents.parse(tk.properties["user_agent"])
|
||||
res = render(None, "TrustedDevices/user-agent.html", context={"ua":ua})
|
||||
res = render(None, "TrustedDevices/user-agent.html", context={"ua": ua})
|
||||
return HttpResponse(res)
|
||||
return HttpResponse("")
|
||||
|
||||
|
||||
def trust_device(request):
|
||||
tk = User_Keys.objects.get(id=request.session["td_id"])
|
||||
tk.properties["status"]="trusted"
|
||||
tk = UserKey.objects.get(id=request.session["td_id"])
|
||||
tk.properties["status"] = "trusted"
|
||||
tk.save()
|
||||
del request.session["td_id"]
|
||||
return HttpResponse("OK")
|
||||
|
||||
def checkTrusted(request):
|
||||
|
||||
def check_trusted(request):
|
||||
res = ""
|
||||
id=request.session.get("td_id","")
|
||||
if id!="":
|
||||
id = request.session.get("td_id", "")
|
||||
if id != "":
|
||||
try:
|
||||
tk = User_Keys.objects.get(id=id)
|
||||
if tk.properties["status"] == "trusted": res = "OK"
|
||||
tk = UserKey.objects.get(id=id)
|
||||
if tk.properties["status"] == "trusted":
|
||||
res = "OK"
|
||||
except:
|
||||
pass
|
||||
return HttpResponse(res)
|
||||
|
||||
def getCookie(request):
|
||||
tk = User_Keys.objects.get(id=request.session["td_id"])
|
||||
|
||||
def get_cookie(request):
|
||||
tk = UserKey.objects.get(id=request.session["td_id"])
|
||||
|
||||
if tk.properties["status"] == "trusted":
|
||||
context={"added":True}
|
||||
response = render(request,"TrustedDevices/Done.html", context)
|
||||
from datetime import datetime, timedelta
|
||||
context = {"added": True}
|
||||
response = render(request, "TrustedDevices/Done.html", context)
|
||||
|
||||
expires = datetime.now() + timedelta(days=180)
|
||||
tk.expires=expires
|
||||
tk.expires = expires
|
||||
tk.save()
|
||||
response.set_cookie("deviceid", tk.properties["signature"], expires=expires)
|
||||
return response
|
||||
|
||||
|
||||
def add(request):
|
||||
context=csrf(request)
|
||||
if request.method=="GET":
|
||||
return render(request,"TrustedDevices/Add.html",context)
|
||||
context = csrf(request)
|
||||
if request.method == "GET":
|
||||
return render(request, "TrustedDevices/Add.html", context)
|
||||
else:
|
||||
key=request.POST["key"].replace("-","").replace(" ","").upper()
|
||||
key = request.POST["key"].replace("-", "").replace(" ", "").upper()
|
||||
context["username"] = request.POST["username"]
|
||||
context["key"] = request.POST["key"]
|
||||
trusted_keys=User_Keys.objects.filter(username=request.POST["username"],properties__has="$.key="+key)
|
||||
cookie=False
|
||||
trusted_keys = UserKey.objects.filter(
|
||||
username=request.POST["username"], properties__has="$.key=" + key
|
||||
)
|
||||
cookie = False
|
||||
if trusted_keys.exists():
|
||||
tk=trusted_keys[0]
|
||||
request.session["td_id"]=tk.id
|
||||
ua=request.META['HTTP_USER_AGENT']
|
||||
agent=user_agents.parse(ua)
|
||||
tk = trusted_keys[0]
|
||||
request.session["td_id"] = tk.id
|
||||
ua = request.META["HTTP_USER_AGENT"]
|
||||
agent = user_agents.parse(ua)
|
||||
if agent.is_pc:
|
||||
context["invalid"]="This is a PC, it can't used as a trusted device."
|
||||
context["invalid"] = "This is a PC, it can't used as a trusted device."
|
||||
else:
|
||||
tk.properties["user_agent"]=ua
|
||||
tk.properties["user_agent"] = ua
|
||||
tk.save()
|
||||
context["success"]=True
|
||||
# tk.properties["user_agent"]=ua
|
||||
# tk.save()
|
||||
# context["success"]=True
|
||||
context["success"] = True
|
||||
|
||||
else:
|
||||
context["invalid"]="The username or key is wrong, please check and try again."
|
||||
context[
|
||||
"invalid"
|
||||
] = "The username or key is wrong, please check and try again."
|
||||
|
||||
return render(request, "TrustedDevices/Add.html", context)
|
||||
|
||||
return render(request,"TrustedDevices/Add.html", context)
|
||||
|
||||
def start(request):
|
||||
if User_Keys.objects.filter(username=request.user.username,key_type="Trusted Device").count()>= 2:
|
||||
return render(request,"TrustedDevices/start.html",{"not_allowed":True})
|
||||
td=None
|
||||
if not request.session.get("td_id",None):
|
||||
td=User_Keys()
|
||||
td.username=request.user.username
|
||||
td.properties={"key":id_generator(),"status":"adding"}
|
||||
td.key_type="Trusted Device"
|
||||
if (
|
||||
UserKey.objects.filter(
|
||||
username=request.user.username, key_type="Trusted Device"
|
||||
).count()
|
||||
>= 2
|
||||
):
|
||||
return render(request, "TrustedDevices/start.html", {"not_allowed": True})
|
||||
td = None
|
||||
if not request.session.get("td_id", None):
|
||||
td = UserKey()
|
||||
td.username = request.user.username
|
||||
td.properties = {"key": id_generator(), "status": "adding"}
|
||||
td.key_type = "Trusted Device"
|
||||
td.save()
|
||||
request.session["td_id"]=td.id
|
||||
request.session["td_id"] = td.id
|
||||
try:
|
||||
if td==None: td=User_Keys.objects.get(id=request.session["td_id"])
|
||||
context={"key":td.properties["key"]}
|
||||
if td is None:
|
||||
td = UserKey.objects.get(id=request.session["td_id"])
|
||||
context = {"key": td.properties["key"]}
|
||||
except:
|
||||
del request.session["td_id"]
|
||||
return start(request)
|
||||
return render(request,"TrustedDevices/start.html",context)
|
||||
return render(request, "TrustedDevices/start.html", context)
|
||||
|
||||
|
||||
def send_email(request):
|
||||
body=render(request,"TrustedDevices/email.html",{}).content
|
||||
from .Common import send
|
||||
e=request.user.email
|
||||
if e=="":
|
||||
e=request.session.get("user",{}).get("email","")
|
||||
if e=="":
|
||||
body = render(request, "TrustedDevices/email.html", {}).content
|
||||
e = request.user.email
|
||||
if e == "":
|
||||
e = request.session.get("user", {}).get("email", "")
|
||||
if e == "":
|
||||
res = "User has no email on the system."
|
||||
elif send([e],"Add Trusted Device Link",body):
|
||||
res="Sent Successfully"
|
||||
elif send([e], "Add Trusted Device Link", body):
|
||||
res = "Sent Successfully"
|
||||
else:
|
||||
res="Error occured, please try again later."
|
||||
res = "Error occured, please try again later."
|
||||
return HttpResponse(res)
|
||||
|
||||
|
||||
def verify(request):
|
||||
if request.COOKIES.get('deviceid',None):
|
||||
from jose import jwt
|
||||
json= jwt.decode(request.COOKIES.get('deviceid'),settings.SECRET_KEY)
|
||||
if json["username"].lower()== request.session['base_username'].lower():
|
||||
if request.COOKIES.get("deviceid", None):
|
||||
json = jwt.decode(request.COOKIES.get("deviceid"), settings.SECRET_KEY)
|
||||
if json["username"].lower() == request.session["base_username"].lower():
|
||||
try:
|
||||
uk = User_Keys.objects.get(username=request.POST["username"].lower(), properties__has="$.key=" + json["key"])
|
||||
uk = UserKey.objects.get(
|
||||
username=request.POST["username"].lower(),
|
||||
properties__has="$.key=" + json["key"],
|
||||
)
|
||||
if uk.enabled and uk.properties["status"] == "trusted":
|
||||
uk.last_used=timezone.now()
|
||||
uk.last_used = timezone.now()
|
||||
uk.save()
|
||||
request.session["mfa"] = {"verified": True, "method": "Trusted Device","id":uk.id}
|
||||
request.session["mfa"] = {
|
||||
"verified": True,
|
||||
"method": "Trusted Device",
|
||||
"id": uk.id,
|
||||
}
|
||||
return True
|
||||
except:
|
||||
return False
|
||||
|
||||
+86
-51
@@ -1,106 +1,141 @@
|
||||
import datetime
|
||||
import hashlib
|
||||
import random
|
||||
import time
|
||||
|
||||
from u2flib_server.u2f import (begin_registration, begin_authentication,
|
||||
complete_registration, complete_authentication)
|
||||
import simplejson
|
||||
from cryptography import x509
|
||||
from cryptography.hazmat.backends import default_backend
|
||||
from cryptography.hazmat.primitives.serialization import Encoding
|
||||
from django.shortcuts import render
|
||||
import simplejson
|
||||
#from django.template.context import RequestContext
|
||||
from django.template.context_processors import csrf
|
||||
from django.conf import settings
|
||||
from django.http import HttpResponse
|
||||
from .models import *
|
||||
from .views import login
|
||||
from django.http import HttpResponse, JsonResponse
|
||||
from django.shortcuts import render
|
||||
from django.template.context_processors import csrf
|
||||
from django.utils import timezone
|
||||
from u2flib_server.u2f import (
|
||||
begin_authentication,
|
||||
begin_registration,
|
||||
complete_authentication,
|
||||
complete_registration,
|
||||
)
|
||||
|
||||
from .Common import get_redirect_url
|
||||
from .models import UserKey
|
||||
from .views import login
|
||||
|
||||
|
||||
def recheck(request):
|
||||
context = csrf(request)
|
||||
context["mode"]="recheck"
|
||||
context["mode"] = "recheck"
|
||||
s = sign(request.user.username)
|
||||
request.session["_u2f_challenge_"] = s[0]
|
||||
context["token"] = s[1]
|
||||
request.session["mfa_recheck"]=True
|
||||
return render(request,"U2F/recheck.html", context)
|
||||
request.session["mfa_recheck"] = True
|
||||
return render(request, "U2F/recheck.html", context)
|
||||
|
||||
|
||||
def process_recheck(request):
|
||||
x=validate(request,request.user.username)
|
||||
if x==True:
|
||||
return HttpResponse(simplejson.dumps({"recheck":True}),content_type="application/json")
|
||||
x = validate(request, request.user.username)
|
||||
if x is True:
|
||||
request.session["mfa"]["rechecked_at"] = time.time()
|
||||
return JsonResponse({"recheck": True})
|
||||
return x
|
||||
|
||||
|
||||
def check_errors(request, data):
|
||||
if "errorCode" in data:
|
||||
if data["errorCode"] == 0: return True
|
||||
if data["errorCode"] == 0:
|
||||
return True
|
||||
if data["errorCode"] == 4:
|
||||
return HttpResponse("Invalid Security Key")
|
||||
if data["errorCode"] == 1:
|
||||
return auth(request)
|
||||
return True
|
||||
def validate(request,username):
|
||||
import datetime, random
|
||||
|
||||
|
||||
def validate(request, username):
|
||||
data = simplejson.loads(request.POST["response"])
|
||||
|
||||
res= check_errors(request,data)
|
||||
if res!=True:
|
||||
res = check_errors(request, data)
|
||||
if res is not True:
|
||||
return res
|
||||
|
||||
challenge = request.session.pop('_u2f_challenge_')
|
||||
challenge = request.session.pop("_u2f_challenge_")
|
||||
device, c, t = complete_authentication(challenge, data, [settings.U2F_APPID])
|
||||
|
||||
key=User_Keys.objects.get(username=username,properties__shas="$.device.publicKey=%s"%device["publicKey"])
|
||||
key.last_used=timezone.now()
|
||||
key = UserKey.objects.get(
|
||||
username=username,
|
||||
properties__shas="$.device.publicKey=%s" % device["publicKey"],
|
||||
)
|
||||
key.last_used = timezone.now()
|
||||
key.save()
|
||||
mfa = {"verified": True, "method": "U2F","id":key.id}
|
||||
mfa = {"verified": True, "method": "U2F", "id": key.id}
|
||||
if getattr(settings, "MFA_RECHECK", False):
|
||||
mfa["next_check"] = int((datetime.datetime.now()
|
||||
+ datetime.timedelta(
|
||||
seconds=random.randint(settings.MFA_RECHECK_MIN, settings.MFA_RECHECK_MAX))).strftime("%s"))
|
||||
mfa["next_check"] = datetime.datetime.timestamp(
|
||||
(
|
||||
datetime.datetime.now()
|
||||
+ datetime.timedelta(
|
||||
seconds=random.randint(
|
||||
settings.MFA_RECHECK_MIN, settings.MFA_RECHECK_MAX
|
||||
)
|
||||
)
|
||||
)
|
||||
)
|
||||
request.session["mfa"] = mfa
|
||||
return True
|
||||
|
||||
def auth(request):
|
||||
context=csrf(request)
|
||||
s=sign(request.session["base_username"])
|
||||
request.session["_u2f_challenge_"]=s[0]
|
||||
context["token"]=s[1]
|
||||
|
||||
return render(request,"U2F/Auth.html")
|
||||
def auth(request):
|
||||
context = csrf(request)
|
||||
s = sign(request.session["base_username"])
|
||||
request.session["_u2f_challenge_"] = s[0]
|
||||
context["token"] = s[1]
|
||||
|
||||
return render(request, "U2F/Auth.html")
|
||||
|
||||
|
||||
def start(request):
|
||||
enroll = begin_registration(settings.U2F_APPID, [])
|
||||
request.session['_u2f_enroll_'] = enroll.json
|
||||
context=csrf(request)
|
||||
context["token"]=simplejson.dumps(enroll.data_for_client)
|
||||
return render(request,"U2F/Add.html",context)
|
||||
request.session["_u2f_enroll_"] = enroll.json
|
||||
context = csrf(request)
|
||||
context["token"] = simplejson.dumps(enroll.data_for_client)
|
||||
context.update(get_redirect_url())
|
||||
return render(request, "U2F/Add.html", context)
|
||||
|
||||
|
||||
def bind(request):
|
||||
import hashlib
|
||||
enroll = request.session['_u2f_enroll_']
|
||||
data=simplejson.loads(request.POST["response"])
|
||||
enroll = request.session["_u2f_enroll_"]
|
||||
data = simplejson.loads(request.POST["response"])
|
||||
device, cert = complete_registration(enroll, data, [settings.U2F_APPID])
|
||||
cert = x509.load_der_x509_certificate(cert, default_backend())
|
||||
cert_hash=hashlib.md5(cert.public_bytes(Encoding.PEM)).hexdigest()
|
||||
q=User_Keys.objects.filter(key_type="U2F", properties__icontains= cert_hash)
|
||||
cert_hash = hashlib.md5(cert.public_bytes(Encoding.PEM)).hexdigest()
|
||||
q = UserKey.objects.filter(key_type="U2F", properties__icontains=cert_hash)
|
||||
if q.exists():
|
||||
return HttpResponse("This key is registered before, it can't be registered again.")
|
||||
User_Keys.objects.filter(username=request.user.username,key_type="U2F").delete()
|
||||
uk = User_Keys()
|
||||
return HttpResponse(
|
||||
"This key is registered before, it can't be registered again."
|
||||
)
|
||||
UserKey.objects.filter(username=request.user.username, key_type="U2F").delete()
|
||||
uk = UserKey()
|
||||
uk.username = request.user.username
|
||||
uk.properties = {"device":simplejson.loads(device.json),"cert":cert_hash}
|
||||
uk.owned_by_enterprise = getattr(settings, "MFA_OWNED_BY_ENTERPRISE", False)
|
||||
uk.properties = {"device": simplejson.loads(device.json), "cert": cert_hash}
|
||||
uk.key_type = "U2F"
|
||||
uk.save()
|
||||
return HttpResponse("OK")
|
||||
|
||||
|
||||
def sign(username):
|
||||
u2f_devices=[d.properties["device"] for d in User_Keys.objects.filter(username=username,key_type="U2F")]
|
||||
u2f_devices = [
|
||||
d.properties["device"]
|
||||
for d in UserKey.objects.filter(username=username, key_type="U2F")
|
||||
]
|
||||
challenge = begin_authentication(settings.U2F_APPID, u2f_devices)
|
||||
return [challenge.json,simplejson.dumps(challenge.data_for_client)]
|
||||
return [challenge.json, simplejson.dumps(challenge.data_for_client)]
|
||||
|
||||
|
||||
def verify(request):
|
||||
x= validate(request,request.session["base_username"])
|
||||
if x==True:
|
||||
x = validate(request, request.session["base_username"])
|
||||
if x is True:
|
||||
return login(request)
|
||||
else: return x
|
||||
else:
|
||||
return x
|
||||
|
||||
+1
-1
@@ -1 +1 @@
|
||||
__version__="1.6.0"
|
||||
__version__ = "2.2.0"
|
||||
|
||||
@@ -1,3 +0,0 @@
|
||||
from django.contrib import admin
|
||||
|
||||
# Register your models here.
|
||||
+4
-2
@@ -1,4 +1,6 @@
|
||||
from django.apps import AppConfig
|
||||
|
||||
|
||||
class myAppNameConfig(AppConfig):
|
||||
name = 'mfa'
|
||||
verbose_name = 'A Much Better Name'
|
||||
name = "mfa"
|
||||
verbose_name = "A Much Better Name"
|
||||
|
||||
+23
-23
@@ -1,32 +1,32 @@
|
||||
import pyotp
|
||||
from .models import *
|
||||
from . import TrustedDevice, U2F, FIDO2, totp
|
||||
import simplejson
|
||||
from django.shortcuts import HttpResponse
|
||||
from mfa.views import verify,goto
|
||||
def has_mfa(request,username):
|
||||
if User_Keys.objects.filter(username=username,enabled=1).count()>0:
|
||||
from django.http import JsonResponse
|
||||
|
||||
from . import FIDO2, U2F, TrustedDevice, totp
|
||||
from .models import UserKey
|
||||
from .views import verify
|
||||
|
||||
|
||||
def has_mfa(request, username):
|
||||
if UserKey.objects.filter(username=username, enabled=1).count() > 0:
|
||||
return verify(request, username)
|
||||
return False
|
||||
|
||||
def is_mfa(request,ignore_methods=[]):
|
||||
if request.session.get("mfa",{}).get("verified",False):
|
||||
if not request.session.get("mfa",{}).get("method",None) in ignore_methods:
|
||||
|
||||
def is_mfa(request, ignore_methods=[]):
|
||||
if request.session.get("mfa", {}).get("verified", False):
|
||||
if not request.session.get("mfa", {}).get("method", None) in ignore_methods:
|
||||
return True
|
||||
return False
|
||||
|
||||
|
||||
def recheck(request):
|
||||
method=request.session.get("mfa",{}).get("method",None)
|
||||
method = request.session.get("mfa", {}).get("method", None)
|
||||
if not method:
|
||||
return HttpResponse(simplejson.dumps({"res":False}),content_type="application/json")
|
||||
if method=="Trusted Device":
|
||||
return HttpResponse(simplejson.dumps({"res":TrustedDevice.verify(request)}),content_type="application/json")
|
||||
elif method=="U2F":
|
||||
return HttpResponse(simplejson.dumps({"html": U2F.recheck(request).content}), content_type="application/json")
|
||||
return JsonResponse({"res": False})
|
||||
if method == "Trusted Device":
|
||||
return JsonResponse({"res": TrustedDevice.verify(request)})
|
||||
elif method == "U2F":
|
||||
return JsonResponse({"html": U2F.recheck(request).content})
|
||||
elif method == "FIDO2":
|
||||
return HttpResponse(simplejson.dumps({"html": FIDO2.recheck(request).content}), content_type="application/json")
|
||||
elif method=="TOTP":
|
||||
return HttpResponse(simplejson.dumps({"html": totp.recheck(request).content}), content_type="application/json")
|
||||
|
||||
|
||||
|
||||
return JsonResponse({"html": FIDO2.recheck(request).content})
|
||||
elif method == "TOTP":
|
||||
return JsonResponse({"html": totp.recheck(request).content})
|
||||
|
||||
+15
-8
@@ -1,13 +1,20 @@
|
||||
import time
|
||||
from django.http import HttpResponseRedirect
|
||||
from django.core.urlresolvers import reverse
|
||||
|
||||
from django.conf import settings
|
||||
from django.http import HttpResponseRedirect
|
||||
from django.urls import reverse
|
||||
|
||||
|
||||
def process(request):
|
||||
next_check=request.session.get('mfa',{}).get("next_check",False)
|
||||
if not next_check: return None
|
||||
now=int(time.time())
|
||||
next_check = request.session.get("mfa", {}).get("next_check", False)
|
||||
if not next_check:
|
||||
return None
|
||||
now = int(time.time())
|
||||
if now >= next_check:
|
||||
method=request.session["mfa"]["method"]
|
||||
method = request.session["mfa"]["method"]
|
||||
path = request.META["PATH_INFO"]
|
||||
return HttpResponseRedirect(reverse(method+"_auth")+"?next=%s"%(settings.BASE_URL + path).replace("//", "/"))
|
||||
return None
|
||||
return HttpResponseRedirect(
|
||||
reverse(method + "_auth")
|
||||
+ "?next=%s" % (settings.BASE_URL + path).replace("//", "/")
|
||||
)
|
||||
return None
|
||||
|
||||
@@ -6,17 +6,24 @@ from django.db import models, migrations
|
||||
|
||||
class Migration(migrations.Migration):
|
||||
|
||||
dependencies = [
|
||||
]
|
||||
dependencies = []
|
||||
|
||||
operations = [
|
||||
migrations.CreateModel(
|
||||
name='User_Keys',
|
||||
name="User_Keys",
|
||||
fields=[
|
||||
('id', models.AutoField(verbose_name='ID', serialize=False, auto_created=True, primary_key=True)),
|
||||
('username', models.CharField(max_length=50)),
|
||||
('secret_key', models.CharField(max_length=15)),
|
||||
('added_on', models.DateTimeField(auto_now_add=True)),
|
||||
(
|
||||
"id",
|
||||
models.AutoField(
|
||||
verbose_name="ID",
|
||||
serialize=False,
|
||||
auto_created=True,
|
||||
primary_key=True,
|
||||
),
|
||||
),
|
||||
("username", models.CharField(max_length=50)),
|
||||
("secret_key", models.CharField(max_length=15)),
|
||||
("added_on", models.DateTimeField(auto_now_add=True)),
|
||||
],
|
||||
),
|
||||
]
|
||||
|
||||
@@ -7,13 +7,13 @@ from django.db import models, migrations
|
||||
class Migration(migrations.Migration):
|
||||
|
||||
dependencies = [
|
||||
('mfa', '0001_initial'),
|
||||
("mfa", "0001_initial"),
|
||||
]
|
||||
|
||||
operations = [
|
||||
migrations.AddField(
|
||||
model_name='user_keys',
|
||||
name='key_type',
|
||||
field=models.CharField(default=b'TOTP', max_length=25),
|
||||
model_name="user_keys",
|
||||
name="key_type",
|
||||
field=models.CharField(default=b"TOTP", max_length=25),
|
||||
),
|
||||
]
|
||||
|
||||
@@ -7,13 +7,13 @@ from django.db import models, migrations
|
||||
class Migration(migrations.Migration):
|
||||
|
||||
dependencies = [
|
||||
('mfa', '0002_user_keys_key_type'),
|
||||
("mfa", "0002_user_keys_key_type"),
|
||||
]
|
||||
|
||||
operations = [
|
||||
migrations.AlterField(
|
||||
model_name='user_keys',
|
||||
name='secret_key',
|
||||
model_name="user_keys",
|
||||
name="secret_key",
|
||||
field=models.CharField(max_length=32),
|
||||
),
|
||||
]
|
||||
|
||||
@@ -7,13 +7,13 @@ from django.db import models, migrations
|
||||
class Migration(migrations.Migration):
|
||||
|
||||
dependencies = [
|
||||
('mfa', '0003_auto_20181114_2159'),
|
||||
("mfa", "0003_auto_20181114_2159"),
|
||||
]
|
||||
|
||||
operations = [
|
||||
migrations.AddField(
|
||||
model_name='user_keys',
|
||||
name='enabled',
|
||||
model_name="user_keys",
|
||||
name="enabled",
|
||||
field=models.BooleanField(default=True),
|
||||
),
|
||||
]
|
||||
|
||||
@@ -7,24 +7,25 @@ import jsonfield.fields
|
||||
|
||||
def modify_json(apps, schema_editor):
|
||||
from django.conf import settings
|
||||
|
||||
if "mysql" in settings.DATABASES.get("default", {}).get("engine", ""):
|
||||
migrations.RunSQL("alter table mfa_user_keys modify column properties json;")
|
||||
|
||||
|
||||
class Migration(migrations.Migration):
|
||||
dependencies = [
|
||||
('mfa', '0004_user_keys_enabled'),
|
||||
("mfa", "0004_user_keys_enabled"),
|
||||
]
|
||||
|
||||
operations = [
|
||||
migrations.RemoveField(
|
||||
model_name='user_keys',
|
||||
name='secret_key',
|
||||
model_name="user_keys",
|
||||
name="secret_key",
|
||||
),
|
||||
migrations.AddField(
|
||||
model_name='user_keys',
|
||||
name='properties',
|
||||
model_name="user_keys",
|
||||
name="properties",
|
||||
field=jsonfield.fields.JSONField(null=True),
|
||||
),
|
||||
migrations.RunPython(modify_json)
|
||||
migrations.RunPython(modify_json),
|
||||
]
|
||||
|
||||
@@ -7,21 +7,29 @@ from django.db import models, migrations
|
||||
class Migration(migrations.Migration):
|
||||
|
||||
dependencies = [
|
||||
('mfa', '0005_auto_20181115_2014'),
|
||||
("mfa", "0005_auto_20181115_2014"),
|
||||
]
|
||||
|
||||
operations = [
|
||||
migrations.CreateModel(
|
||||
name='Trusted_Devices',
|
||||
name="Trusted_Devices",
|
||||
fields=[
|
||||
('id', models.AutoField(verbose_name='ID', serialize=False, auto_created=True, primary_key=True)),
|
||||
('signature', models.CharField(max_length=255)),
|
||||
('key', models.CharField(max_length=6)),
|
||||
('username', models.CharField(max_length=50)),
|
||||
('user_agent', models.CharField(max_length=255)),
|
||||
('status', models.CharField(default=b'adding', max_length=255)),
|
||||
('added_on', models.DateTimeField(auto_now_add=True)),
|
||||
('last_used', models.DateTimeField(default=None, null=True)),
|
||||
(
|
||||
"id",
|
||||
models.AutoField(
|
||||
verbose_name="ID",
|
||||
serialize=False,
|
||||
auto_created=True,
|
||||
primary_key=True,
|
||||
),
|
||||
),
|
||||
("signature", models.CharField(max_length=255)),
|
||||
("key", models.CharField(max_length=6)),
|
||||
("username", models.CharField(max_length=50)),
|
||||
("user_agent", models.CharField(max_length=255)),
|
||||
("status", models.CharField(default=b"adding", max_length=255)),
|
||||
("added_on", models.DateTimeField(auto_now_add=True)),
|
||||
("last_used", models.DateTimeField(default=None, null=True)),
|
||||
],
|
||||
),
|
||||
]
|
||||
|
||||
@@ -7,16 +7,16 @@ from django.db import models, migrations
|
||||
class Migration(migrations.Migration):
|
||||
|
||||
dependencies = [
|
||||
('mfa', '0006_trusted_devices'),
|
||||
("mfa", "0006_trusted_devices"),
|
||||
]
|
||||
|
||||
operations = [
|
||||
migrations.DeleteModel(
|
||||
name='Trusted_Devices',
|
||||
name="Trusted_Devices",
|
||||
),
|
||||
migrations.AddField(
|
||||
model_name='user_keys',
|
||||
name='expires',
|
||||
model_name="user_keys",
|
||||
name="expires",
|
||||
field=models.DateTimeField(default=None, null=True, blank=True),
|
||||
),
|
||||
]
|
||||
|
||||
@@ -7,13 +7,13 @@ from django.db import models, migrations
|
||||
class Migration(migrations.Migration):
|
||||
|
||||
dependencies = [
|
||||
('mfa', '0007_auto_20181230_1549'),
|
||||
("mfa", "0007_auto_20181230_1549"),
|
||||
]
|
||||
|
||||
operations = [
|
||||
migrations.AddField(
|
||||
model_name='user_keys',
|
||||
name='last_used',
|
||||
model_name="user_keys",
|
||||
name="last_used",
|
||||
field=models.DateTimeField(default=None, null=True, blank=True),
|
||||
),
|
||||
]
|
||||
|
||||
@@ -0,0 +1,28 @@
|
||||
# -*- coding: utf-8 -*-
|
||||
from __future__ import unicode_literals
|
||||
|
||||
from django.db import models, migrations
|
||||
from django.conf import settings
|
||||
|
||||
|
||||
def update_owned_by_enterprise(apps, schema_editor):
|
||||
user_keys = apps.get_model("mfa", "user_keys")
|
||||
user_keys.objects.filter(key_type="FIDO2").update(
|
||||
owned_by_enterprise=getattr(settings, "MFA_OWNED_BY_ENTERPRISE", False)
|
||||
)
|
||||
|
||||
|
||||
class Migration(migrations.Migration):
|
||||
|
||||
dependencies = [
|
||||
("mfa", "0008_user_keys_last_used"),
|
||||
]
|
||||
|
||||
operations = [
|
||||
migrations.AddField(
|
||||
model_name="user_keys",
|
||||
name="owned_by_enterprise",
|
||||
field=models.NullBooleanField(default=None),
|
||||
),
|
||||
migrations.RunPython(update_owned_by_enterprise),
|
||||
]
|
||||
@@ -0,0 +1,18 @@
|
||||
# Generated by Django 2.0 on 2020-11-10 05:57
|
||||
|
||||
from django.db import migrations, models
|
||||
|
||||
|
||||
class Migration(migrations.Migration):
|
||||
|
||||
dependencies = [
|
||||
("mfa", "0009_user_keys_owned_by_enterprise"),
|
||||
]
|
||||
|
||||
operations = [
|
||||
migrations.AlterField(
|
||||
model_name="user_keys",
|
||||
name="key_type",
|
||||
field=models.CharField(default="TOTP", max_length=25),
|
||||
),
|
||||
]
|
||||
@@ -0,0 +1,18 @@
|
||||
# Generated by Django 2.2 on 2021-05-30 06:22
|
||||
|
||||
from django.db import migrations, models
|
||||
|
||||
|
||||
class Migration(migrations.Migration):
|
||||
|
||||
dependencies = [
|
||||
("mfa", "0010_auto_20201110_0557"),
|
||||
]
|
||||
|
||||
operations = [
|
||||
migrations.AlterField(
|
||||
model_name="user_keys",
|
||||
name="owned_by_enterprise",
|
||||
field=models.BooleanField(blank=True, default=None, null=True),
|
||||
),
|
||||
]
|
||||
@@ -0,0 +1,17 @@
|
||||
# Generated by Django 3.2.4 on 2021-06-23 07:10
|
||||
|
||||
from django.db import migrations
|
||||
|
||||
|
||||
class Migration(migrations.Migration):
|
||||
|
||||
dependencies = [
|
||||
("mfa", "0011_auto_20210530_0622"),
|
||||
]
|
||||
|
||||
operations = [
|
||||
migrations.RenameModel(
|
||||
old_name="User_Keys",
|
||||
new_name="UserKey",
|
||||
),
|
||||
]
|
||||
@@ -0,0 +1,35 @@
|
||||
# Generated by Django 2.2 on 2021-06-24 15:05
|
||||
|
||||
from django.db import migrations, models
|
||||
|
||||
|
||||
class Migration(migrations.Migration):
|
||||
|
||||
dependencies = [
|
||||
("mfa", "0012_rename_user_keys_userkey"),
|
||||
]
|
||||
|
||||
operations = [
|
||||
migrations.CreateModel(
|
||||
name="OTPTracker",
|
||||
fields=[
|
||||
(
|
||||
"id",
|
||||
models.AutoField(
|
||||
auto_created=True,
|
||||
primary_key=True,
|
||||
serialize=False,
|
||||
verbose_name="ID",
|
||||
),
|
||||
),
|
||||
("actor", models.CharField(max_length=50)),
|
||||
("value", models.CharField(max_length=6)),
|
||||
("success", models.BooleanField(blank=True)),
|
||||
("done_on", models.DateTimeField(auto_now=True)),
|
||||
],
|
||||
),
|
||||
migrations.AddIndex(
|
||||
model_name="otptracker",
|
||||
index=models.Index(fields=["actor"], name="mfa_otptrac_usernam_1f423f_idx"),
|
||||
),
|
||||
]
|
||||
+41
-21
@@ -1,25 +1,45 @@
|
||||
from django.db import models
|
||||
from jsonfield import JSONField
|
||||
from jose import jwt
|
||||
from django.conf import settings
|
||||
from jsonLookup import shasLookup
|
||||
JSONField.register_lookup(shasLookup)
|
||||
from django.db import models
|
||||
from jose import jwt
|
||||
from jsonfield import JSONField
|
||||
|
||||
|
||||
class UserKey(models.Model):
|
||||
username = models.CharField(max_length=50)
|
||||
properties = JSONField(null=True)
|
||||
added_on = models.DateTimeField(auto_now_add=True)
|
||||
key_type = models.CharField(max_length=25, default="TOTP")
|
||||
enabled = models.BooleanField(default=True)
|
||||
expires = models.DateTimeField(null=True, default=None, blank=True)
|
||||
last_used = models.DateTimeField(null=True, default=None, blank=True)
|
||||
owned_by_enterprise = models.BooleanField(default=None, null=True, blank=True)
|
||||
|
||||
def save(self, *args, **kwargs):
|
||||
if (
|
||||
self.key_type == "Trusted Device"
|
||||
and self.properties.get("signature", "") == ""
|
||||
):
|
||||
self.properties["signature"] = jwt.encode(
|
||||
{"username": self.username, "key": self.properties["key"]},
|
||||
settings.SECRET_KEY,
|
||||
)
|
||||
super().save(*args, **kwargs)
|
||||
|
||||
class User_Keys(models.Model):
|
||||
username=models.CharField(max_length = 50)
|
||||
properties=JSONField(null = True)
|
||||
added_on=models.DateTimeField(auto_now_add = True)
|
||||
key_type=models.CharField(max_length = 25,default = "TOTP")
|
||||
enabled=models.BooleanField(default=True)
|
||||
expires=models.DateTimeField(null=True,default=None,blank=True)
|
||||
last_used=models.DateTimeField(null=True,default=None,blank=True)
|
||||
def save(self, force_insert=False, force_update=False, using=None, update_fields=None):
|
||||
if self.key_type == "Trusted Device" and self.properties.get("signature","") == "":
|
||||
self.properties["signature"]= jwt.encode({"username": self.username, "key": self.properties["key"]}, settings.SECRET_KEY)
|
||||
super(User_Keys, self).save(force_insert=force_insert, force_update=force_update, using=using, update_fields=update_fields)
|
||||
def __unicode__(self):
|
||||
return "%s -- %s"%(self.username,self.key_type)
|
||||
def __str__(self):
|
||||
return self.__unicode__()
|
||||
return "%s -- %s" % (self.username, self.key_type)
|
||||
|
||||
class Meta:
|
||||
app_label='mfa'
|
||||
app_label = "mfa"
|
||||
|
||||
|
||||
class OTPTracker(models.Model):
|
||||
actor = models.CharField(
|
||||
max_length=50, help_text="Username"
|
||||
) # named this way for indexing purpose.
|
||||
value = models.CharField(max_length=6)
|
||||
success = models.BooleanField(blank=True)
|
||||
done_on = models.DateTimeField(auto_now=True)
|
||||
|
||||
class Meta:
|
||||
app_label = "mfa"
|
||||
indexes = [models.Index(fields=["actor"])]
|
||||
|
||||
Vendored
+9
File diff suppressed because one or more lines are too long
@@ -2,54 +2,50 @@
|
||||
{% block head %}
|
||||
{% endblock %}
|
||||
{% block content %}
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
<div class="panel panel-default">
|
||||
<div class="panel-heading">
|
||||
<strong> Activate Token by email</strong>
|
||||
</div>
|
||||
<div class="panel-body">
|
||||
|
||||
<br/>
|
||||
<br/>
|
||||
<div class="container">
|
||||
<div class="panel panel-default">
|
||||
<div class="panel-heading">
|
||||
<strong> Activate Token by email</strong>
|
||||
</div>
|
||||
<div class="panel-body">
|
||||
<FORM METHOD="POST" ACTION="{% url 'start_email' %}" Id="formLogin" onSubmit="" name="FrontPage_Form1">
|
||||
|
||||
|
||||
{% csrf_token %}
|
||||
{% if invalid %}
|
||||
<div class="alert alert-danger">
|
||||
Sorry, The provided token is not valid.
|
||||
{% csrf_token %}
|
||||
{% if invalid %}
|
||||
<div class="alert alert-danger">
|
||||
Sorry, The provided token is not valid.
|
||||
</div>
|
||||
{% endif %}
|
||||
{% if quota %}
|
||||
<div class="alert alert-warning">
|
||||
{{ quota }}
|
||||
</div>
|
||||
{% endif %}
|
||||
<fieldset>
|
||||
<div class="row">
|
||||
<div class="col-sm-12 col-md-12">
|
||||
<p>Enter the code sent to your email.</p>
|
||||
</div>
|
||||
</div>
|
||||
{% endif %}
|
||||
{% if quota %}
|
||||
<div class="alert alert-warning">
|
||||
{{ quota }}
|
||||
<div class="row">
|
||||
<div class="col-sm-12 col-md-12">
|
||||
<div class="form-group">
|
||||
<div class="input-group">
|
||||
<span class="input-group-addon">
|
||||
<i class="glyphicon glyphicon-lock"></i>
|
||||
</span>
|
||||
<input class="form-control" size="6" MaxLength="6" value="" placeholder="e.g 55552" name="otp" type="text" id="otp" autofocus>
|
||||
</div>
|
||||
</div>
|
||||
<div class="form-group">
|
||||
<input type="submit" class="btn btn-lg btn-success btn-block" value="Verify">
|
||||
</div>
|
||||
</div>
|
||||
</div>
|
||||
{% endif %}
|
||||
<fieldset>
|
||||
<div class="row">
|
||||
<div class="col-sm-12 col-md-12">
|
||||
<p>Enter the 6-digits sent to your email.</p>
|
||||
</div>
|
||||
</div>
|
||||
|
||||
<div class="row">
|
||||
<div class="col-sm-12 col-md-12">
|
||||
<div class="form-group">
|
||||
<div class="input-group">
|
||||
<span class="input-group-addon">
|
||||
<i class="glyphicon glyphicon-lock"></i>
|
||||
</span>
|
||||
<input class="form-control" size="6" MaxLength="6" value="" placeholder="e.g 55552" name="otp" type="text" id="otp" autofocus>
|
||||
|
||||
</div>
|
||||
</div>
|
||||
|
||||
<div class="form-group">
|
||||
|
||||
<input type="submit" class="btn btn-lg btn-success btn-block" value="Verify">
|
||||
</div>
|
||||
</div>
|
||||
</fieldset>
|
||||
</fieldset>
|
||||
</FORM>
|
||||
</div>
|
||||
</div>
|
||||
</div>
|
||||
</div>
|
||||
{% endblock %}
|
||||
@@ -39,7 +39,7 @@
|
||||
<fieldset>
|
||||
<div class="row">
|
||||
<div class="col-sm-12 col-md-12">
|
||||
<p>Enter the 6-digits sent to your email.</p>
|
||||
<p>Enter the code sent to your email.</p>
|
||||
</div>
|
||||
</div>
|
||||
|
||||
|
||||
@@ -2,6 +2,7 @@
|
||||
{% load static %}
|
||||
{% block head %}
|
||||
<script type="application/javascript" src="{% static 'mfa/js/cbor.js'%}"></script>
|
||||
<script type="application/javascript" src="{% static 'mfa/js/ua-parser.min.js'%}"></script>
|
||||
<script type="application/javascript">
|
||||
function begin_reg(){
|
||||
fetch('{% url 'fido2_begin_reg' %}',{}).then(function(response) {
|
||||
@@ -31,7 +32,7 @@
|
||||
}).then(function (res)
|
||||
{
|
||||
if (res["status"] =='OK')
|
||||
$("#res").html("<div class='alert alert-success'>Registered Successfully, <a href='{% url 'mfa_home' %}'> Go to Security Home</a></div>")
|
||||
$("#res").html("<div class='alert alert-success'>Registered Successfully, <a href='{{redirect_html}}'> {{reg_success_msg}}</a></div>")
|
||||
else
|
||||
$("#res").html("<div class='alert alert-danger'>Registeration Failed as " + res["message"] + ", <a href='javascript:void(0)' onclick='begin_reg()'> try again or <a href='{% url 'mfa_home' %}'> Go to Security Home</a></div>")
|
||||
|
||||
@@ -40,7 +41,17 @@
|
||||
$("#res").html("<div class='alert alert-danger'>Registeration Failed as " +reason +", <a href='javascript:void(0)' onclick='begin_reg()'> try again </a> or <a href='{% url 'mfa_home' %}'> Go to Security Home</a></div>")
|
||||
})
|
||||
}
|
||||
$(document).ready(setTimeout(begin_reg,500))
|
||||
$(document).ready(function (){
|
||||
ua=new UAParser().getResult()
|
||||
if (ua.browser.name == "Safari")
|
||||
{
|
||||
$("#res").html("<button class='btn btn-success' onclick='begin_reg()'>Start...</button>")
|
||||
}
|
||||
else
|
||||
{
|
||||
setTimeout(begin_reg, 500)
|
||||
}
|
||||
})
|
||||
</script>
|
||||
|
||||
{% endblock %}
|
||||
@@ -55,8 +66,8 @@
|
||||
<div class="panel-body">
|
||||
|
||||
|
||||
<div class="row alert alert-pr" id="res">
|
||||
<p style="color: green">Your broswer should ask you to confirm you indentity.</p>
|
||||
<div class="row alert alert-pr" id="res" align="center">
|
||||
<p style="color: green">Your browser should ask you to confirm you identity.</p>
|
||||
|
||||
</div>
|
||||
</div>
|
||||
|
||||
@@ -1,6 +1,4 @@
|
||||
{% extends "mfa_auth_base.html" %}
|
||||
{% block content %}
|
||||
<br/>
|
||||
<br/>
|
||||
{% include 'FIDO2/recheck.html' with mode='auth' %}
|
||||
{% endblock %}
|
||||
@@ -1,5 +1,6 @@
|
||||
{% load static %}
|
||||
<script type="application/javascript" src="{% static 'mfa/js/cbor.js' %}"></script>
|
||||
<script type="application/javascript" src="{% static 'mfa/js/ua-parser.min.js' %}"></script>
|
||||
<div class="row">
|
||||
|
||||
<div class="col-sm-10 col-sm-offset-1 col-xs-12 col-md-10 col-md-offset-1 col-lg-8 col-lg-offset-2">
|
||||
@@ -17,11 +18,14 @@
|
||||
<br/>
|
||||
|
||||
{% endif %}
|
||||
<p style="color: green">please press the button on your security key to prove it is you.</p>
|
||||
<div id="res">
|
||||
<p style="color: green">please press the button on your security key to prove it is you.</p>
|
||||
</div>
|
||||
<div id="msgdiv"></div>
|
||||
{% if mode == "auth" %}
|
||||
<form id="u2f_login" action="{% url 'fido2_complete_auth' %}" method="post" enctype="multipart/form-data">
|
||||
{% elif mode == "recheck" %}
|
||||
<form id="u2f_login" action="{% url 'u2f_recheck' %}" method="post">
|
||||
<form id="u2f_login" action="{% url 'fido2_recheck' %}" method="post" enctype="multipart/form-data">
|
||||
{% endif %}
|
||||
{% csrf_token %}
|
||||
<input type="hidden" name="response" id="response" value=""/>
|
||||
@@ -71,17 +75,22 @@
|
||||
}).then(function (response) {if (response.ok) return res = response.json()}).then(function (res) {
|
||||
if (res.status=="OK")
|
||||
{
|
||||
$("#msgdiv").addClass("alert alert-success").removeClass("alert-danger")
|
||||
$("#msgdiv").html("Verified....please wait")
|
||||
{% if mode == "auth" %}
|
||||
window.location.href=res.redirect;
|
||||
{% elif mode == "recheck" %}
|
||||
mfa_success_function();
|
||||
mfa_success_function();
|
||||
{% endif %}
|
||||
}
|
||||
else {
|
||||
$("#msgdiv").addClass("alert alert-danger").removeClass("alert-success")
|
||||
$("#msgdiv").html("Verification Failed as " + res.message + ", <a href='javascript:void(0)' onclick='authen())'> try again</a> or <a href='javascript:void(0)' onclick='history.back()'> Go Back</a>")
|
||||
|
||||
{% if mode == "auth" %}
|
||||
alert("Error occured, please try again")
|
||||
login()
|
||||
|
||||
{% elif mode == "recheck" %}
|
||||
|
||||
mfa_failed_function();
|
||||
{% endif %}
|
||||
}
|
||||
@@ -95,7 +104,11 @@
|
||||
$("#main_paragraph").addClass("alert alert-danger")
|
||||
$("#main_paragraph").html("FIDO2 must work under secure context")
|
||||
} else {
|
||||
authen()
|
||||
ua=new UAParser().getResult()
|
||||
if (ua.browser.name == "Safari")
|
||||
$("#res").html("<button class='btn btn-success' onclick='authen()'>Authenticate...</button>")
|
||||
else
|
||||
authen()
|
||||
}
|
||||
});
|
||||
|
||||
|
||||
@@ -20,7 +20,7 @@
|
||||
$("#modal-footer").prepend("<button id='actionBtn' class='btn btn-danger' onclick='confirmDel("+id+")'>Confirm Deletion</button>")
|
||||
$("#popUpModal").modal()
|
||||
}
|
||||
{% if not HIDE_DISABLE %}
|
||||
|
||||
function toggleKey(id) {
|
||||
$.ajax({
|
||||
url:"{% url 'toggle_key' %}?id="+id,
|
||||
@@ -34,7 +34,6 @@
|
||||
}
|
||||
})
|
||||
}
|
||||
{% endif %}
|
||||
</script>
|
||||
<link href="{% static 'mfa/css/bootstrap-toggle.min.css' %}" rel="stylesheet">
|
||||
<script src="{% static 'mfa/js/bootstrap-toggle.min.js'%}"></script>
|
||||
@@ -67,7 +66,7 @@
|
||||
{% endif %}
|
||||
</ul>
|
||||
</div>
|
||||
|
||||
</div>
|
||||
<br/>
|
||||
<br/>
|
||||
<table class="table table-striped">
|
||||
|
||||
+28
-28
@@ -2,7 +2,7 @@
|
||||
{% extends "base.html" %}
|
||||
{% load static %}
|
||||
{% block head %}
|
||||
<style>
|
||||
<style>
|
||||
#two-factor-steps {
|
||||
border: 1px solid #ccc;
|
||||
border-radius: 3px;
|
||||
@@ -12,8 +12,8 @@
|
||||
margin: 0px;
|
||||
}
|
||||
</style>
|
||||
<script src="{% static 'mfa/js/qrious.min.js' %}" type="text/javascript"></script>
|
||||
<script type="text/javascript">
|
||||
<script src="{% static 'mfa/js/qrious.min.js' %}" type="text/javascript"></script>
|
||||
<script type="text/javascript">
|
||||
var key="";
|
||||
$(document).ready(function addToken() {
|
||||
$.ajax({
|
||||
@@ -43,7 +43,7 @@
|
||||
else
|
||||
{
|
||||
alert("Your authenticator is added successfully.")
|
||||
window.location.href="{% url 'mfa_home' %}"
|
||||
window.location.href="{{ redirect_html }}"
|
||||
}
|
||||
}
|
||||
})
|
||||
@@ -61,49 +61,49 @@
|
||||
</script>
|
||||
{% endblock %}
|
||||
{% block content %}
|
||||
<br/>
|
||||
<br/>
|
||||
<div class="container">
|
||||
<div class="col-md-6 col-md-offset-3" id="two-factor-steps">
|
||||
<div class="row" align="center">
|
||||
<h4>Adding Authenticator</h4>
|
||||
</div>
|
||||
<div class="row">
|
||||
<br/>
|
||||
<br/>
|
||||
<div class="container">
|
||||
<div class="col-md-6 col-md-offset-3" id="two-factor-steps">
|
||||
<div class="row" align="center">
|
||||
<h4>Adding Authenticator</h4>
|
||||
</div>
|
||||
<div class="row">
|
||||
|
||||
<p>Scan the image below with the two-factor authentication app on your <a href="javascript:void(0)" onclick="showTOTP()">phone/PC</a> phone/PC. If you can’t use a barcode,
|
||||
<a href="javascript:void(0)" onclick="showKey()">enter this text</a> instead. </p>
|
||||
<p>Scan the image below with the two-factor authentication app on your <a href="javascript:void(0)" onclick="showTOTP()">phone/PC</a>. If you can’t use a barcode,
|
||||
<a href="javascript:void(0)" onclick="showKey()">enter this text</a> instead. </p>
|
||||
</div>
|
||||
|
||||
<div class="row">
|
||||
|
||||
<div align="center" style="display: none" id="second_step">
|
||||
<div align="center" style="display: none" id="second_step">
|
||||
|
||||
<img id="qr"/>
|
||||
<img id="qr"/>
|
||||
|
||||
</div>
|
||||
<div class="row">
|
||||
<div class="row">
|
||||
|
||||
<p><b>Enter the six-digit code from the application</b></p>
|
||||
<p style="color: #333333;font-size: 10px">After scanning the barcode image, the app will display a six-digit code that you can enter below. </p>
|
||||
|
||||
</div>
|
||||
</div>
|
||||
<div class="row">
|
||||
|
||||
|
||||
<input style="display: inline;width: 95%" maxlength="6" size="6" class="form-control" id="answer" placeholder="e.g 785481"/>
|
||||
<input style="display: inline;width: 95%" maxlength="6" size="6" class="form-control" id="answer" placeholder="e.g 785481"/>
|
||||
|
||||
</div>
|
||||
<div class="row">
|
||||
<div class="col-md-6" style="padding-left: 0px">
|
||||
<button class="btn btn-success" onclick="verify()">Enable</button>
|
||||
</div>
|
||||
<div class="col-md-6" align="right" style="padding-right: 30px">
|
||||
<a href="{% url 'mfa_home' %}"><button class="btn btn-default">Cancel</button></a>
|
||||
<div class="row" style="padding-top: 10px;">
|
||||
<div class="col-md-6" style="padding-left: 0px">
|
||||
<button class="btn btn-success" onclick="verify()">Enable</button>
|
||||
</div>
|
||||
<div class="col-md-6" align="right" style="padding-right: 30px">
|
||||
<a href="{% url 'mfa_home' %}"><button class="btn btn-default">Cancel</button></a>
|
||||
</div>
|
||||
</div>
|
||||
</div>
|
||||
</div>
|
||||
|
||||
</div>
|
||||
</div>
|
||||
{% include "modal.html" %}
|
||||
</div>
|
||||
{% include "modal.html" %}
|
||||
{% endblock %}
|
||||
@@ -28,7 +28,7 @@
|
||||
{% csrf_token %}
|
||||
{% if invalid %}
|
||||
<div class="alert alert-danger">
|
||||
Sorry, The provided token is not valid.
|
||||
{{ invalid_msg }}
|
||||
</div>
|
||||
{% endif %}
|
||||
{% if quota %}
|
||||
|
||||
@@ -24,7 +24,7 @@
|
||||
if (data == "OK")
|
||||
{
|
||||
alert("Your device is added successfully.")
|
||||
window.location.href="{% url 'mfa_home' %}"
|
||||
window.location.href="{{ redirect_html }}"
|
||||
}
|
||||
}
|
||||
})
|
||||
|
||||
@@ -1,3 +0,0 @@
|
||||
from django.test import TestCase
|
||||
|
||||
# Create your tests here.
|
||||
+96
-46
@@ -1,70 +1,120 @@
|
||||
from django.shortcuts import render
|
||||
from django.http import HttpResponse
|
||||
from .models import *
|
||||
from django.template.context_processors import csrf
|
||||
import simplejson
|
||||
from django.template.context import RequestContext
|
||||
from django.conf import settings
|
||||
import pyotp
|
||||
from .views import login
|
||||
import datetime
|
||||
from django.utils import timezone
|
||||
import random
|
||||
def verify_login(request,username,token):
|
||||
for key in User_Keys.objects.filter(username=username,key_type = "TOTP"):
|
||||
import time
|
||||
|
||||
import pyotp
|
||||
from django.conf import settings
|
||||
from django.http import HttpResponse, JsonResponse
|
||||
from django.shortcuts import render
|
||||
from django.template.context_processors import csrf
|
||||
from django.utils import timezone
|
||||
from django.views.decorators.cache import never_cache
|
||||
|
||||
from .Common import get_redirect_url
|
||||
from .models import UserKey, OTPTracker
|
||||
from .views import login
|
||||
|
||||
|
||||
def verify_login(request, username, token):
|
||||
FAILURE_LIMIT = getattr("settings", "MFA_TOTP_FAILURE_LIMIT", 3)
|
||||
start_time = timezone.now() + datetime.timedelta(
|
||||
minutes=-1 * getattr(settings, "MFA_TOTP_FAILURE_WINDOW", 5)
|
||||
)
|
||||
if (
|
||||
OTPTracker.objects.filter(
|
||||
done_on__gt=start_time, actor=username, success=0
|
||||
).count()
|
||||
>= FAILURE_LIMIT
|
||||
):
|
||||
return [
|
||||
False,
|
||||
"Using this method is temporarily suspended on your account, use another method, or later again later ",
|
||||
]
|
||||
for key in UserKey.objects.filter(username=username, key_type="TOTP"):
|
||||
totp = pyotp.TOTP(key.properties["secret_key"])
|
||||
if totp.verify(token,valid_window = 30):
|
||||
key.last_used=timezone.now()
|
||||
if totp.verify(token, valid_window=30):
|
||||
if OTPTracker.objects.filter(actor=username, value=token).exists():
|
||||
return [
|
||||
False,
|
||||
"This code is used before, please generate another token",
|
||||
]
|
||||
OTPTracker.objects.create(actor=username, value=token, success=True)
|
||||
key.last_used = timezone.now()
|
||||
key.save()
|
||||
return [True,key.id]
|
||||
return [False]
|
||||
return [True, key.id]
|
||||
OTPTracker.objects.create(actor=username, value=token, success=False)
|
||||
return [False, "Invalid Token"]
|
||||
|
||||
|
||||
def recheck(request):
|
||||
context = csrf(request)
|
||||
context["mode"]="recheck"
|
||||
context["mode"] = "recheck"
|
||||
if request.method == "POST":
|
||||
if verify_login(request,request.user.username, token=request.POST["otp"]):
|
||||
return HttpResponse(simplejson.dumps({"recheck": True}), content_type="application/json")
|
||||
if verify_login(request, request.user.username, token=request.POST["otp"]):
|
||||
request.session["mfa"]["rechecked_at"] = time.time()
|
||||
return JsonResponse({"recheck": True})
|
||||
else:
|
||||
return HttpResponse(simplejson.dumps({"recheck": False}), content_type="application/json")
|
||||
return render(request,"TOTP/recheck.html", context)
|
||||
return JsonResponse({"recheck": False})
|
||||
return render(request, "TOTP/recheck.html", context)
|
||||
|
||||
|
||||
@never_cache
|
||||
def auth(request):
|
||||
context=csrf(request)
|
||||
if request.method=="POST":
|
||||
res=verify_login(request,request.session["base_username"],token = request.POST["otp"])
|
||||
context = csrf(request)
|
||||
if request.method == "POST":
|
||||
res = verify_login(
|
||||
request, request.session["base_username"], token=request.POST["otp"]
|
||||
)
|
||||
if res[0]:
|
||||
mfa = {"verified": True, "method": "TOTP","id":res[1]}
|
||||
mfa = {"verified": True, "method": "TOTP", "id": res[1]}
|
||||
if getattr(settings, "MFA_RECHECK", False):
|
||||
mfa["next_check"] = int((datetime.datetime.now()
|
||||
+ datetime.timedelta(
|
||||
seconds=random.randint(settings.MFA_RECHECK_MIN, settings.MFA_RECHECK_MAX))).strftime("%s"))
|
||||
mfa["next_check"] = datetime.datetime.timestamp(
|
||||
(
|
||||
datetime.datetime.now()
|
||||
+ datetime.timedelta(
|
||||
seconds=random.randint(
|
||||
settings.MFA_RECHECK_MIN, settings.MFA_RECHECK_MAX
|
||||
)
|
||||
)
|
||||
)
|
||||
)
|
||||
request.session["mfa"] = mfa
|
||||
return login(request)
|
||||
context["invalid"]=True
|
||||
return render(request,"TOTP/Auth.html", context)
|
||||
context["invalid"] = True
|
||||
context["invalid_msg"] = res[1]
|
||||
return render(request, "TOTP/Auth.html", context)
|
||||
|
||||
|
||||
|
||||
def getToken(request):
|
||||
secret_key=pyotp.random_base32()
|
||||
def get_token(request):
|
||||
secret_key = pyotp.random_base32()
|
||||
totp = pyotp.TOTP(secret_key)
|
||||
request.session["new_mfa_answer"]=totp.now()
|
||||
return HttpResponse(simplejson.dumps({"qr":pyotp.totp.TOTP(secret_key).provisioning_uri(str(request.user.username), issuer_name = settings.TOKEN_ISSUER_NAME),
|
||||
"secret_key": secret_key}))
|
||||
request.session["new_mfa_answer"] = totp.now()
|
||||
return JsonResponse(
|
||||
{
|
||||
"qr": pyotp.totp.TOTP(secret_key).provisioning_uri(
|
||||
str(request.user.username), issuer_name=settings.TOKEN_ISSUER_NAME
|
||||
),
|
||||
"secret_key": secret_key,
|
||||
}
|
||||
)
|
||||
|
||||
|
||||
def verify(request):
|
||||
answer=request.GET["answer"]
|
||||
secret_key=request.GET["key"]
|
||||
answer = request.GET["answer"]
|
||||
secret_key = request.GET["key"]
|
||||
totp = pyotp.TOTP(secret_key)
|
||||
if totp.verify(answer,valid_window = 60):
|
||||
uk=User_Keys()
|
||||
uk.username=request.user.username
|
||||
uk.properties={"secret_key":secret_key}
|
||||
#uk.name="Authenticatior #%s"%User_Keys.objects.filter(username=user.username,type="TOTP")
|
||||
uk.key_type="TOTP"
|
||||
if totp.verify(answer, valid_window=60):
|
||||
uk = UserKey()
|
||||
uk.username = request.user.username
|
||||
uk.properties = {"secret_key": secret_key}
|
||||
uk.key_type = "TOTP"
|
||||
uk.save()
|
||||
return HttpResponse("Success")
|
||||
else: return HttpResponse("Error")
|
||||
else:
|
||||
return HttpResponse("Error")
|
||||
|
||||
|
||||
@never_cache
|
||||
def start(request):
|
||||
return render(request,"TOTP/Add.html",{})
|
||||
"""Start Adding Time One Time Password (TOTP)"""
|
||||
return render(request, "TOTP/Add.html", get_redirect_url())
|
||||
|
||||
+39
-51
@@ -1,53 +1,41 @@
|
||||
from . import views,totp,U2F,TrustedDevice,helpers,FIDO2,Email
|
||||
#app_name='mfa'
|
||||
from django.urls import path
|
||||
|
||||
from . import FIDO2, U2F, Email, TrustedDevice, helpers, totp, views
|
||||
|
||||
try:
|
||||
from django.urls import re_path as url
|
||||
except:
|
||||
from django.conf.urls import url
|
||||
urlpatterns = [
|
||||
url(r'totp/start/', totp.start , name="start_new_otop"),
|
||||
url(r'totp/getToken', totp.getToken , name="get_new_otop"),
|
||||
url(r'totp/verify', totp.verify, name="verify_otop"),
|
||||
url(r'totp/auth', totp.auth, name="totp_auth"),
|
||||
url(r'totp/recheck', totp.recheck, name="totp_recheck"),
|
||||
|
||||
url(r'email/start/', Email.start , name="start_email"),
|
||||
url(r'email/auth/', Email.auth , name="email_auth"),
|
||||
|
||||
url(r'u2f/$', U2F.start, name="start_u2f"),
|
||||
url(r'u2f/bind', U2F.bind, name="bind_u2f"),
|
||||
url(r'u2f/auth', U2F.auth, name="u2f_auth"),
|
||||
url(r'u2f/process_recheck', U2F.process_recheck, name="u2f_recheck"),
|
||||
url(r'u2f/verify', U2F.verify, name="u2f_verify"),
|
||||
|
||||
url(r'fido2/$', FIDO2.start, name="start_fido2"),
|
||||
url(r'fido2/auth', FIDO2.auth, name="fido2_auth"),
|
||||
url(r'fido2/begin_auth', FIDO2.authenticate_begin, name="fido2_begin_auth"),
|
||||
url(r'fido2/complete_auth', FIDO2.authenticate_complete, name="fido2_complete_auth"),
|
||||
url(r'fido2/begin_reg', FIDO2.begin_registeration, name="fido2_begin_reg"),
|
||||
url(r'fido2/complete_reg', FIDO2.complete_reg, name="fido2_complete_reg"),
|
||||
url(r'u2f/bind', U2F.bind, name="bind_u2f"),
|
||||
url(r'u2f/auth', U2F.auth, name="u2f_auth"),
|
||||
url(r'u2f/process_recheck', U2F.process_recheck, name="u2f_recheck"),
|
||||
url(r'u2f/verify', U2F.verify, name="u2f_verify"),
|
||||
|
||||
|
||||
url(r'td/$', TrustedDevice.start, name="start_td"),
|
||||
url(r'td/add', TrustedDevice.add, name="add_td"),
|
||||
url(r'td/send_link', TrustedDevice.send_email, name="td_sendemail"),
|
||||
url(r'td/get-ua', TrustedDevice.getUserAgent, name="td_get_useragent"),
|
||||
url(r'td/trust', TrustedDevice.trust_device, name="td_trust_device"),
|
||||
url(r'u2f/checkTrusted', TrustedDevice.checkTrusted, name="td_checkTrusted"),
|
||||
url(r'u2f/secure_device', TrustedDevice.getCookie, name="td_securedevice"),
|
||||
|
||||
url(r'^$', views.index, name="mfa_home"),
|
||||
url(r'goto/(.*)', views.goto, name="mfa_goto"),
|
||||
url(r'selct_method', views.show_methods, name="mfa_methods_list"),
|
||||
url(r'recheck', helpers.recheck, name="mfa_recheck"),
|
||||
url(r'toggleKey', views.toggleKey, name="toggle_key"),
|
||||
url(r'delete', views.delKey, name="mfa_delKey"),
|
||||
url(r'reset', views.reset_cookie, name="mfa_reset_cookie"),
|
||||
|
||||
]
|
||||
# print(urlpatterns)
|
||||
path("totp/start/", totp.start, name="start_new_otop"),
|
||||
path("totp/getToken/", totp.get_token, name="get_new_otop"),
|
||||
path("totp/verify/", totp.verify, name="verify_otop"),
|
||||
path("totp/auth/", totp.auth, name="totp_auth"),
|
||||
path("totp/recheck/", totp.recheck, name="totp_recheck"),
|
||||
path("email/start/", Email.start, name="start_email"),
|
||||
path("email/auth/", Email.auth, name="email_auth"),
|
||||
path("u2f/", U2F.start, name="start_u2f"),
|
||||
path("u2f/bind/", U2F.bind, name="bind_u2f"),
|
||||
path("u2f/auth/", U2F.auth, name="u2f_auth"),
|
||||
path("u2f/process_recheck/", U2F.process_recheck, name="u2f_recheck"),
|
||||
path("u2f/verify/", U2F.verify, name="u2f_verify"),
|
||||
path("fido2/", FIDO2.start, name="start_fido2"),
|
||||
path("fido2/auth/", FIDO2.auth, name="fido2_auth"),
|
||||
path("fido2/begin_auth/", FIDO2.authenticate_begin, name="fido2_begin_auth"),
|
||||
path(
|
||||
"fido2/complete_auth/", FIDO2.authenticate_complete, name="fido2_complete_auth"
|
||||
),
|
||||
path("fido2/begin_reg/", FIDO2.begin_registeration, name="fido2_begin_reg"),
|
||||
path("fido2/complete_reg/", FIDO2.complete_reg, name="fido2_complete_reg"),
|
||||
path("fido2/recheck/", FIDO2.recheck, name="fido2_recheck"),
|
||||
path("td/", TrustedDevice.start, name="start_td"),
|
||||
path("td/add/", TrustedDevice.add, name="add_td"),
|
||||
path("td/send_link/", TrustedDevice.send_email, name="td_sendemail"),
|
||||
path("td/get-ua/", TrustedDevice.get_user_agent, name="td_get_useragent"),
|
||||
path("td/trust/", TrustedDevice.trust_device, name="td_trust_device"),
|
||||
path("u2f/checkTrusted/", TrustedDevice.check_trusted, name="td_checkTrusted"),
|
||||
path("u2f/secure_device", TrustedDevice.get_cookie, name="td_securedevice"),
|
||||
path("", views.index, name="mfa_home"),
|
||||
path("goto/<method>/", views.goto, name="mfa_goto"),
|
||||
path("selct_method/", views.show_methods, name="mfa_methods_list"),
|
||||
path("recheck/", helpers.recheck, name="mfa_recheck"),
|
||||
path("toggleKey/", views.toggle_key, name="toggle_key"),
|
||||
path("delete/", views.del_key, name="mfa_delKey"),
|
||||
path("reset/", views.reset_cookie, name="mfa_reset_cookie"),
|
||||
]
|
||||
|
||||
+64
-50
@@ -1,90 +1,104 @@
|
||||
from django.shortcuts import render
|
||||
#from django.http import HttpResponse,HttpResponseRedirect
|
||||
from .models import *
|
||||
try:
|
||||
from django.urls import reverse
|
||||
except:
|
||||
from django.core.urlresolvers import reverse
|
||||
from django.template.context_processors import csrf
|
||||
from django.template.context import RequestContext
|
||||
from django.http import HttpResponseRedirect
|
||||
import importlib
|
||||
|
||||
from django.conf import settings
|
||||
from . import TrustedDevice
|
||||
from django.contrib.auth.decorators import login_required
|
||||
from django.http import HttpResponse, HttpResponseRedirect
|
||||
from django.shortcuts import render
|
||||
from django.urls import reverse
|
||||
from user_agents import parse
|
||||
|
||||
from . import TrustedDevice
|
||||
from .models import UserKey
|
||||
|
||||
|
||||
@login_required
|
||||
def index(request):
|
||||
keys=[]
|
||||
context={"keys":User_Keys.objects.filter(username=request.user.username),"UNALLOWED_AUTHEN_METHODS":settings.MFA_UNALLOWED_METHODS
|
||||
,"HIDE_DISABLE":getattr(settings,"MFA_HIDE_DISABLE",[])}
|
||||
keys = []
|
||||
context = {
|
||||
"keys": UserKey.objects.filter(username=request.user.username),
|
||||
"UNALLOWED_AUTHEN_METHODS": settings.MFA_UNALLOWED_METHODS,
|
||||
"HIDE_DISABLE": getattr(settings, "MFA_HIDE_DISABLE", []),
|
||||
}
|
||||
for k in context["keys"]:
|
||||
if k.key_type =="Trusted Device" :
|
||||
setattr(k,"device",parse(k.properties.get("user_agent","-----")))
|
||||
if k.key_type == "Trusted Device":
|
||||
setattr(k, "device", parse(k.properties.get("user_agent", "-----")))
|
||||
elif k.key_type == "FIDO2":
|
||||
setattr(k,"device",k.properties.get("type","----"))
|
||||
setattr(k, "device", k.properties.get("type", "----"))
|
||||
keys.append(k)
|
||||
context["keys"]=keys
|
||||
return render(request,"MFA.html",context)
|
||||
context["keys"] = keys
|
||||
return render(request, "MFA.html", context)
|
||||
|
||||
def verify(request,username):
|
||||
|
||||
def verify(request, username):
|
||||
request.session["base_username"] = username
|
||||
#request.session["base_password"] = password
|
||||
keys=User_Keys.objects.filter(username=username,enabled=1)
|
||||
methods=list(set([k.key_type for k in keys]))
|
||||
keys = UserKey.objects.filter(username=username, enabled=1)
|
||||
methods = list(set([k.key_type for k in keys]))
|
||||
|
||||
if "Trusted Device" in methods and not request.session.get("checked_trusted_device",False):
|
||||
if "Trusted Device" in methods and not request.session.get(
|
||||
"checked_trusted_device", False
|
||||
):
|
||||
if TrustedDevice.verify(request):
|
||||
return login(request)
|
||||
methods.remove("Trusted Device")
|
||||
request.session["mfa_methods"] = methods
|
||||
if len(methods)==1:
|
||||
return HttpResponseRedirect(reverse(methods[0].lower()+"_auth"))
|
||||
if len(methods) == 1:
|
||||
return HttpResponseRedirect(reverse(methods[0].lower() + "_auth"))
|
||||
return show_methods(request)
|
||||
|
||||
|
||||
def show_methods(request):
|
||||
return render(request,"select_mfa_method.html", {})
|
||||
return render(request, "select_mfa_method.html", {})
|
||||
|
||||
|
||||
def reset_cookie(request):
|
||||
response=HttpResponseRedirect(settings.LOGIN_URL)
|
||||
response = HttpResponseRedirect(settings.LOGIN_URL)
|
||||
response.delete_cookie("base_username")
|
||||
return response
|
||||
def login(request):
|
||||
from django.contrib import auth
|
||||
from django.conf import settings
|
||||
callable_func = __get_callable_function__(settings.MFA_LOGIN_CALLBACK)
|
||||
return callable_func(request,username=request.session["base_username"])
|
||||
|
||||
def delKey(request):
|
||||
key=User_Keys.objects.get(id=request.GET["id"])
|
||||
|
||||
def login(request):
|
||||
callable_func = __get_callable_function__(settings.MFA_LOGIN_CALLBACK)
|
||||
return callable_func(request, username=request.session["base_username"])
|
||||
|
||||
|
||||
@login_required
|
||||
def del_key(request):
|
||||
key = UserKey.objects.get(id=request.GET["id"])
|
||||
if key.username == request.user.username:
|
||||
key.delete()
|
||||
return HttpResponse("Deleted Successfully")
|
||||
else:
|
||||
return HttpResponse("Error: You own this token so you can't delete it")
|
||||
|
||||
|
||||
def __get_callable_function__(func_path):
|
||||
import importlib
|
||||
if not '.' in func_path:
|
||||
if "." not in func_path:
|
||||
raise Exception("class Name should include modulename.classname")
|
||||
|
||||
parsed_str = func_path.split(".")
|
||||
module_name , func_name = ".".join(parsed_str[:-1]) , parsed_str[-1]
|
||||
module_name, func_name = ".".join(parsed_str[:-1]), parsed_str[-1]
|
||||
imported_module = importlib.import_module(module_name)
|
||||
callable_func = getattr(imported_module,func_name)
|
||||
callable_func = getattr(imported_module, func_name)
|
||||
if not callable_func:
|
||||
raise Exception("Module does not have requested function")
|
||||
return callable_func
|
||||
|
||||
def toggleKey(request):
|
||||
id=request.GET["id"]
|
||||
q=User_Keys.objects.filter(username=request.user.username, id=id)
|
||||
if q.count()==1:
|
||||
key=q[0]
|
||||
key.enabled=not key.enabled
|
||||
key.save()
|
||||
return HttpResponse("OK")
|
||||
|
||||
@login_required
|
||||
def toggle_key(request):
|
||||
id = request.GET["id"]
|
||||
q = UserKey.objects.filter(username=request.user.username, id=id)
|
||||
if q.count() == 1:
|
||||
key = q[0]
|
||||
if key.key_type not in settings.MFA_HIDE_DISABLE:
|
||||
key.enabled = not key.enabled
|
||||
key.save()
|
||||
return HttpResponse("OK")
|
||||
else:
|
||||
return HttpResponse("You can't change this method.")
|
||||
else:
|
||||
return HttpResponse("Error")
|
||||
|
||||
def goto(request,method):
|
||||
return HttpResponseRedirect(reverse(method.lower()+"_auth"))
|
||||
|
||||
|
||||
def goto(request, method):
|
||||
return HttpResponseRedirect(reverse(method.lower() + "_auth"))
|
||||
|
||||
+1
-1
@@ -2,7 +2,7 @@ site_name: MkLorum
|
||||
nav:
|
||||
- Home: index.md
|
||||
- Installation: installation.md
|
||||
- Code Changes: change_login.md
|
||||
- Code Changes: change_login.md
|
||||
theme: readthedocs
|
||||
markdown_extensions:
|
||||
- fenced_code
|
||||
|
||||
+10
-11
@@ -1,11 +1,10 @@
|
||||
django >= 1.7
|
||||
jsonfield
|
||||
simplejson
|
||||
pyotp
|
||||
python-u2flib-server
|
||||
ua-parser
|
||||
user-agents
|
||||
python-jose
|
||||
fido2 == 0.7
|
||||
jsonLookup
|
||||
|
||||
django >= 2.0
|
||||
jsonfield
|
||||
simplejson
|
||||
pyotp
|
||||
python-u2flib-server
|
||||
ua-parser
|
||||
user-agents
|
||||
python-jose
|
||||
fido2 == 0.9.1
|
||||
jsonLookup
|
||||
|
||||
@@ -3,53 +3,49 @@
|
||||
from setuptools import find_packages, setup
|
||||
|
||||
setup(
|
||||
name='django-mfa2',
|
||||
version='1.6',
|
||||
description='Allows user to add 2FA to their accounts',
|
||||
name="django-mfa2",
|
||||
version="2.2.0",
|
||||
description="Allows user to add 2FA to their accounts",
|
||||
long_description=open("README.md").read(),
|
||||
long_description_content_type="text/markdown",
|
||||
|
||||
author='Mohamed El-Kalioby',
|
||||
author_email = 'mkalioby@mkalioby.com',
|
||||
url = 'https://github.com/mkalioby/django-mfa2/',
|
||||
download_url='https://github.com/mkalioby/django-mfa2/',
|
||||
license='MIT',
|
||||
author="Mohamed El-Kalioby",
|
||||
author_email="mkalioby@mkalioby.com",
|
||||
url="https://github.com/mkalioby/django-mfa2/",
|
||||
download_url="https://github.com/mkalioby/django-mfa2/",
|
||||
license="MIT",
|
||||
packages=find_packages(),
|
||||
install_requires=[
|
||||
'django >= 1.7',
|
||||
'jsonfield',
|
||||
'simplejson',
|
||||
'pyotp',
|
||||
'python-u2flib-server',
|
||||
'ua-parser',
|
||||
'user-agents',
|
||||
'python-jose',
|
||||
'fido2 == 0.7',
|
||||
'jsonLookup'
|
||||
],
|
||||
python_requires=">=2.7, !=3.0.*, !=3.1.*, !=3.2.*, !=3.3.*",
|
||||
"django >= 2.0",
|
||||
"jsonfield",
|
||||
"simplejson",
|
||||
"pyotp",
|
||||
"python-u2flib-server",
|
||||
"ua-parser",
|
||||
"user-agents",
|
||||
"python-jose",
|
||||
"fido2 == 0.9.1",
|
||||
"jsonLookup",
|
||||
],
|
||||
python_requires=">=3.5",
|
||||
include_package_data=True,
|
||||
zip_safe=False, # because we're including static files
|
||||
zip_safe=False, # because we're including static files
|
||||
classifiers=[
|
||||
"Development Status :: 5 - Production/Stable",
|
||||
"Environment :: Web Environment",
|
||||
"Framework :: Django",
|
||||
"Framework :: Django :: 1.7",
|
||||
"Framework :: Django :: 1.8",
|
||||
"Framework :: Django :: 1.9",
|
||||
"Framework :: Django :: 1.10",
|
||||
"Framework :: Django :: 1.11",
|
||||
"Framework :: Django :: 2.0",
|
||||
"Framework :: Django :: 2.1",
|
||||
"Framework :: Django :: 2.2",
|
||||
"Framework :: Django :: 3.0",
|
||||
"Framework :: Django :: 3.1",
|
||||
"Intended Audience :: Developers",
|
||||
"Operating System :: OS Independent",
|
||||
"Programming Language :: Python",
|
||||
"Programming Language :: Python :: 2",
|
||||
"Programming Language :: Python :: 2.7",
|
||||
"Programming Language :: Python :: 3",
|
||||
"Programming Language :: Python :: 3.4",
|
||||
"Programming Language :: Python :: 3.5",
|
||||
"Programming Language :: Python :: 3.6",
|
||||
"Programming Language :: Python :: 3.7",
|
||||
"Programming Language :: Python :: 3.8",
|
||||
"Topic :: Software Development :: Libraries :: Python Modules",
|
||||
]
|
||||
],
|
||||
)
|
||||
|
||||
Reference in New Issue
Block a user